The $10,000 Apple Pay ‘Hack’ That Isn’t Actually a Threat
 Veritasium / YouTube
Veritasium / YouTube
Toggle Dark Mode
A slightly alarming new video is showing how $10,000 could potentially be stolen from a locked iPhone via Apple Pay. However, the good news is that this hack is not only so difficult to pull off as to make it unlikely — it’s also a vulnerability that was discovered five years ago.
Of course, that may not be a good thing, depending on how you look at it. On the one hand, it would be reasonable to expect this flaw to have been patched over the course of five years of security updates. However, the flip side is that the parties involved — Apple and Visa — clearly consider it a non-issue, and they’re not wrong considering that it’s never been exploited in the wild.
The folks at Veritasium teased this reveal in a video two weeks ago, explaining how they’d be doing a follow-up to show how they could snatch $10,000 from Marques Brownlee’s (MKBHD’s) locked iPhone. While I was looking forward to seeing this in action, I also knew what was most likely coming: the Visa Express Transit hack that I wrote about in 2021.
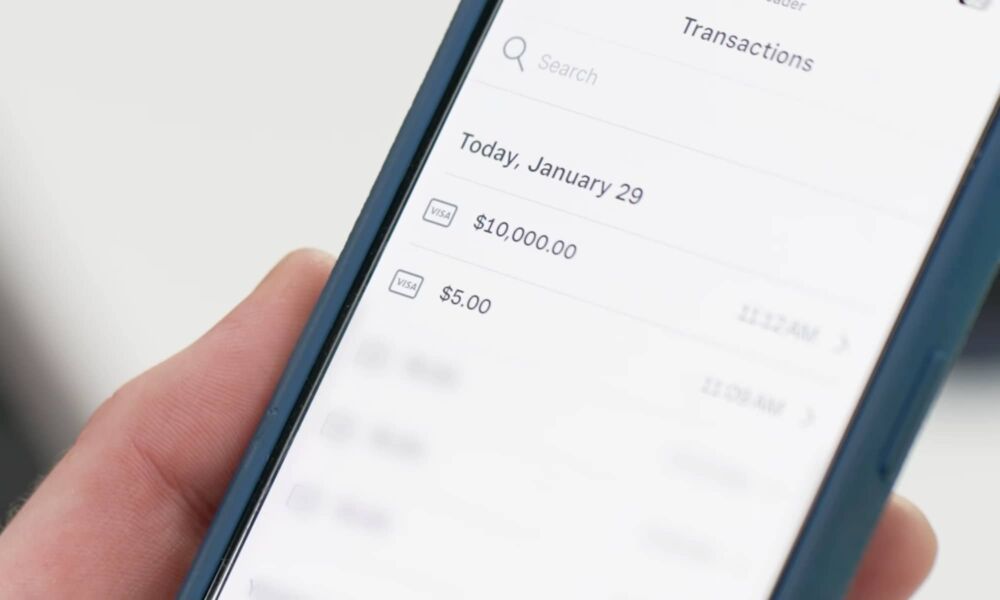
Veritasium didn’t disappoint on either count. The video does indeed show a $10,000 being grabbed from MKBHD’s iPhone, as you can see in the video below.
This is a fun and amusing parlor trick, but it’s also something that’s so unlikely to happen in the real world that neither Apple nor Visa have felt the need to do anything to mitigate it over the past five years.
In other words: Don’t panic. This isn’t something that’s at all likely to happen to you. It’s little more than an interesting theoretical experiment. That said, if you really want to protect yourself against it, the simplest solution is the same recommendation I made five years ago: avoid using a Visa card for Express Transit.
What’s Going on Here?
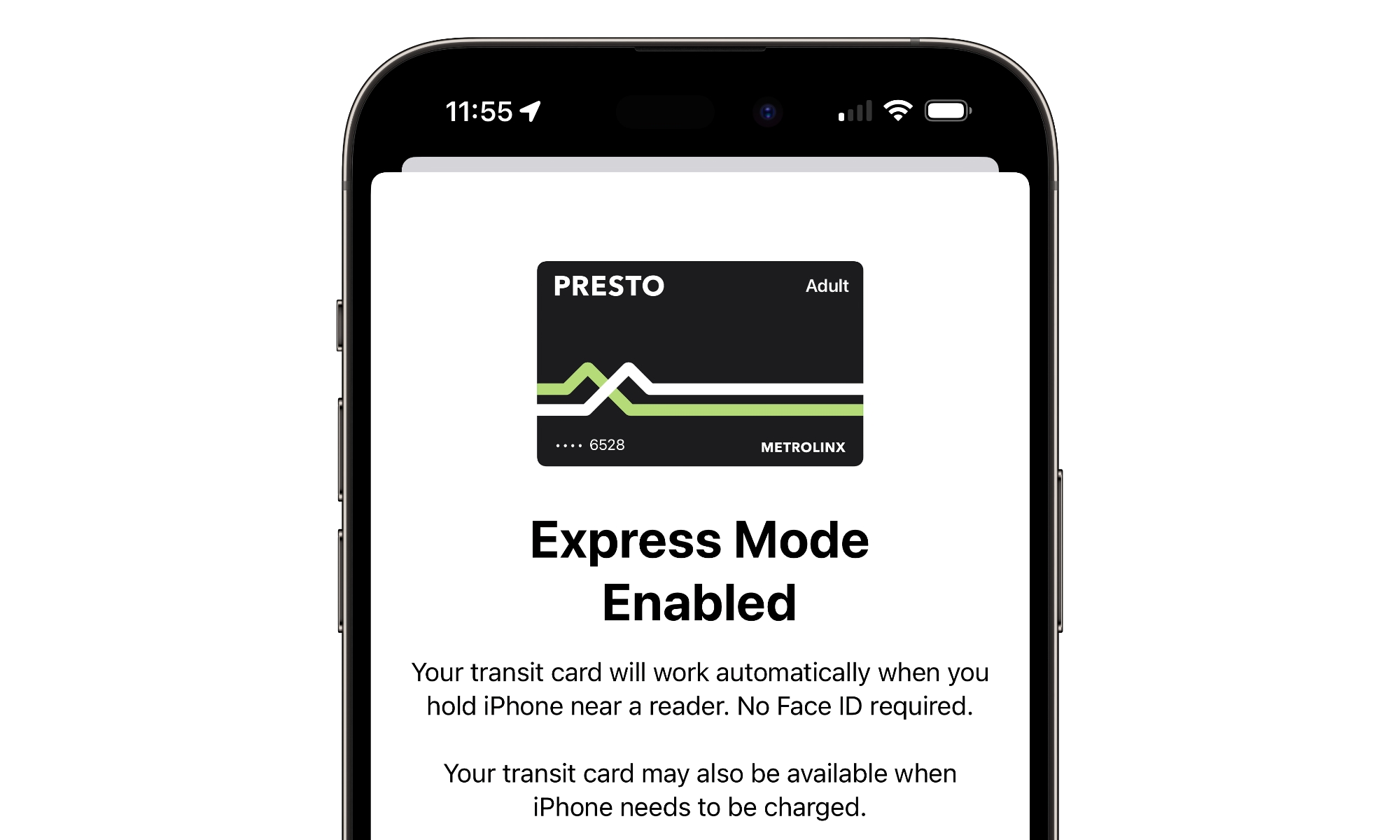
The vulnerability here stems from the fact that Apple’s Express Transit feature is designed to allow Apple Pay to be used for small and authorized transactions while your iPhone or Apple Watch are otherwise locked. This is a convenience feature that lets you quickly pay your fare when getting on a bus or passing through a subway gate.
Express Transit is also very tightly restricted to terminals used by transit systems. There’s a separate authentication handshake with the payment terminal that can’t be used by point-of-sale terminals found anywhere else — and definitely won’t ever be found on mobile payment devices like a Square Reader or Apple’s Tap to Pay on iPhone.
The catch is that while Apple carefully controls the types of terminals that can be authorized for Express Pay, it doesn’t set any limits on the transactions that can pass through. That’s arguably not Apple’s job any more than it is to enforce tap-to-pay limits on traditional terminals. These are set by the card issuers, which is the precise reason why even the normal limits can vary widely between Visa, Mastercard, Amex, and Discover.
In fact, it’s likely that Apple’s agreements with these companies precludes it from taking any role in setting limits. The technology also makes it a challenge since Apple doesn’t actually process the transactions in any way — the transaction passes from the iPhone’s Secure Element to the terminal and over the payment network, just as it would with a physical card. The only place where Apple could get involved would be in refusing to authorize an Express Transit transaction if the amount were over a certain threshold, effectively requiring the user to unlock their iPhone or Apple Watch to proceed.
This is where the method demonstrated by Veritasium comes into play. It’s a “man-in-the-middle” attack that involves using a fake terminal explicitly designed to trigger Express Transit mode on an iPhone and then relaying the Visa credentials to a real payment terminal that can then use them to process a transaction of any amount.
To pull this off, the attacker has to get within about four inches of your iPhone or Apple Watch — about the same distance you’d need to hold your device over a payment terminal. That alone makes it impractical, but Veritasium showed that it also needs to be in contact for more than a split second — a demonstration that actually quells some of the concerns from the original disclosure by security researchers. It’s one of those cases where seeing it play out is actually reassuring because it shows how complicated the whole process is.
It’s also important to note that there’s a time-based factor here. The card information that’s captured by the fake “transit” reader has to be relayed to the remote terminal and used almost immediately. This means the method can’t be used to simply walk around collecting Visa card information from people’s iPhones for later use, which is a much more common approach for professional crooks, who typically sell these credentials on the dark web rather than using them directly.
Should You Be Concerned?
As I said earlier, the complexity and impracticality of this attack makes it a non-issue for most folks, especially since the attack vector requires some pretty precise conditions. It will only work if someone has Express Transit enabled and has a Visa card set up as their Express Transit method. The researchers in 2021 couldn’t make this exploit work with Mastercard, Amex, or Discover, and Veritasium confirms that’s still the case.
To be clear, only one payment card can be assigned to Express Transit. This means that even if you have a Visa card in your Apple Wallet, you won’t be vulnerable to this attack at all if you’re using another type of payment card, either as a primary Express Transit or as a backup for a transit fare card (needless to say, fare cards aren’t vulnerable to this attack either).
While the researchers from the universities of Surrey and Birmingham who discovered this exploit in 2021 expressed concerns that these attacks could “become a real issue” in a few years, we’re now looking at this discovery fading away in the rear-view mirror, and the only report of anyone taking advantage of it has been Veritasium’s video. While that runs the risk of popularizing the technique, this isn’t an attack that novices can easily pull off, and it’s guaranteed the pros have already known about this one for a long time.
Lastly, it’s also notable that Apple and Visa have repeatedly dismissed this as an issue. From Apple’s perspective, it’s Visa’s responsibility, and as far as Visa is concerned, it’s a nothing burger. The credit card company has clearly said that cardholders are protected by its zero liability policy, which means it’s the one taking all the risk.
Visa cards connected to Apple Pay Express Transit are secure, and cardholders should continue to use them with confidence. Variations of contactless fraud schemes have been studied in laboratory settings for more than a decade and have proven to be impractical to execute at scale in the real world.
Visa
Nevertheless, you can check your Express Transit configuration by going to Settings > Wallet & Apple Pay > Express Transit Card. From here, you can select a specific card to use for Express Transit, or choose “None” to disable it entirely. You can do the same for your Apple Watch from the Watch app on your iPhone. Even though you’re extremely unlikely to fall prey to this attack, there’s also not much point in leaving Express Transit on if you don’t use a public transit system that supports Apple Pay.