macOS Bug Allows Any Password to Unlock App Store Preferences
 MacRumors
MacRumors
Toggle Dark Mode
A new bug has been discovered within the latest version of macOS High Sierra that allows the App Store preferences menu to be unlocked with any password.
The potential security vulnerability was uploaded in a post to Open Radar, a forum for community bug report. And while the true seriousness of the exploit is up for debate, it’s still a security hole that needs to be patched.
The bug only seems to affect macOS High Sierra 10.13.2. iDrop News was unable to reproduce the vulnerability in earlier versions of macOS or OS X.
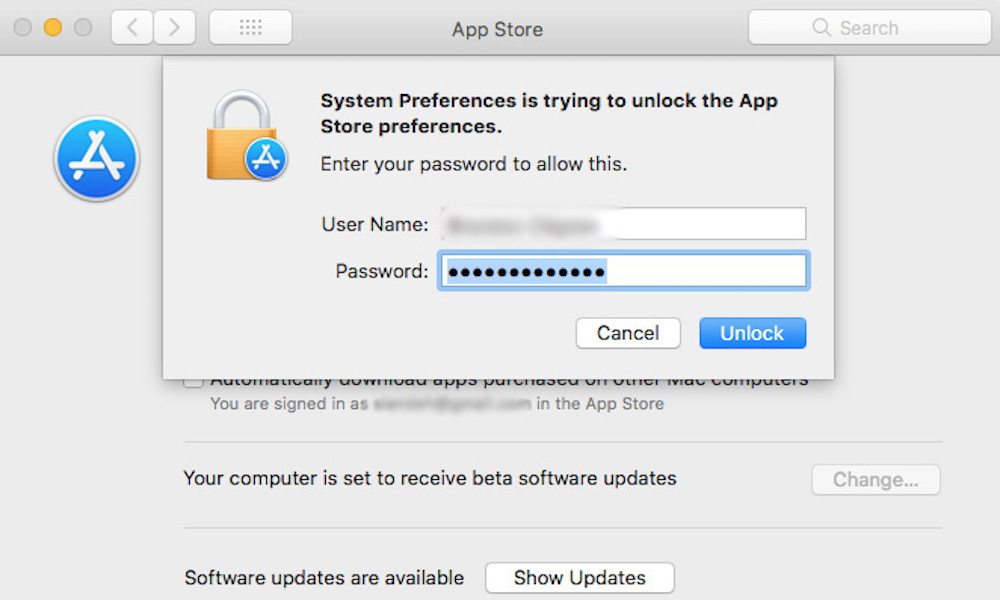
Basically, the vulnerability exists in the System Preferences app, and affects the App Store preferences menu. To make changes to these preferences, one would normally click the padlock icon and input an administrator password. But in the latest macOS High Sierra update, App Store preferences can be accessed by typing anything into the password field and hitting “unlock.”
On the other hand, a user must be logged into an administrator account to access the bug. However, without the need to type in an administrator’s password, the vulnerability could allow malicious entities with access to a Mac to make unwanted changes to App Store preferences.
Thankfully, the bug only seems to affect the App Store preferences menu. Still, administrator accounts can enable or disable a range of settings concerning app updates, macOS updates, and even system data files. Worryingly, the exploit could allow changes to automatic security updates that could patch the flaw.
This isn’t the first time macOS High Sierra has run into password-related problems. In November, a more critical vulnerability was discovered in macOS 10.13.1 that could have allowed attackers to gain root access to a Mac system with a blank password. Apple promptly fixed the exploit with a supplemental update.
In a public apology for the exploit, Apple said it would be “auditing” its development process to help prevent similar vulnerabilities. It is worth noting that App Store preferences are unlocked by default on administrator accounts. But any macOS password-related bug paints Apple’s development process in a bad light, so Cupertino will probably want to patch this security flaw in a public release as quickly as possible.
It does seem that Apple has patched the vulnerability in the latest beta versions of the upcoming macOS High Sierra 10.13.3. But, at this point, it’s not clear whether Apple is going to issue a supplemental update or is simply going to wait for the public release of that macOS version.






