Apple Fixes Major macOS Security Flaw Allowing Admin Access without a Password
 Gadget Hacks
Gadget Hacks
Toggle Dark Mode
Apple’s latest operating system — macOS High Sierra — had a major vulnerability in regards to security: computers running macOS 10.13.1 or earlier could be accessed without a password. While the security flaw appears to require physical access to the device, it was still a major issue since the flaw provided access to the “root” user, allowing full system control including the ability to change passwords, delete and create files, and… well… pretty much anything.
Wednesday morning, Apple released a security update for affected users and has said it will push the security patch automatically later today. Apple released the following statement:
“Security is a top priority for every Apple product, and regrettably we stumbled with this release of macOS. When our security engineers became aware of the issue Tuesday afternoon, we immediately began working on an update that closes the security hole. This morning, as of 8:00 a.m., the update is available for download, and starting later today it will be automatically installed on all systems running the latest version (10.13.1) of macOS High Sierra. We greatly regret this error and we apologize to all Mac users, both for releasing with this vulnerability and for the concern it has caused. Our customers deserve better. We are auditing our development processes to help prevent this from happening again.”
The security flaw went viral Tuesday morning when security researcher Lemi Orhan Ergin (@lemiorhan) tweeted “Dear @AppleSupport, we noticed a HUGE security issue at [sic] MacOS High Sierra. Anyone can login as “root” with [an] empty password after clicking on [the] login button several times. Are you aware of it @Apple?”
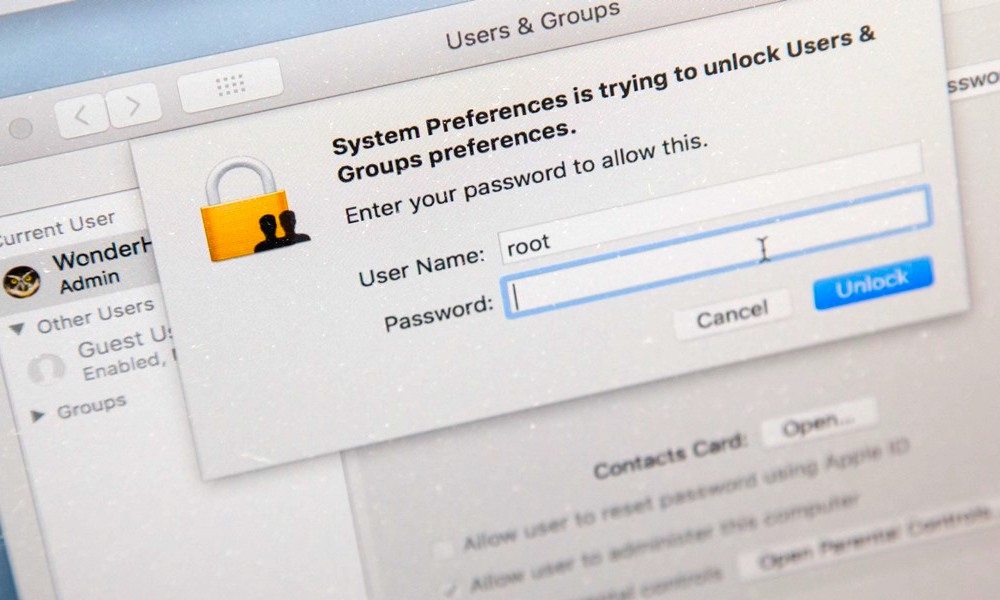
In other words, clicking on the login button (or the unlock button in the login prompts under System Preferences) several times enabled the root user account—which is usually disabled by default for security purposes—with a blank password and then allowed the initiator to login using “root.” While there is some speculation on social media that this could be done remotely, it remains very unlikely and would most likely require a specific setup. The flaw proposed the largest threat to unattended computers and computers in sensitive workplaces such as hospitals and government facilities.
The vulnerability had been reproduced by many individuals online using various versions of macOS High Sierra, but not with versions prior to High Sierra. Apple said in a statement yesterday that they were aware of the issue and were working on a software update to patch it:
“We are working on a software update to address this issue. In the meantime, setting a root password prevents unauthorized access to your Mac. To enable the Root User and set a password, please follow the instructions here. If a Root User is already enabled, to ensure a blank password is not set, please follow the instructions from the ‘Change the root password’ section.”
If you haven’t already we strongly recommend updating to the latest version as soon as possible. While Apple will automatically push the software to any computers it can, it’s best not to take chances. Apple has taken the unique step of adding a bold header to its release notes that say “Install this update as soon as possible.” The full release notes for the patch can be found on Apple’s website.
For security purposes the root user is disabled on your Mac by default. While the patch should be enough for most consumers, for more advanced users—or those in business settings—it may be smart to enable the root user and set a custom password to prevent these kind of issues in the future. If you don’t know your way around a Unix/Linux terminal, here are some step-by-step directions for changing the root password on your device using terminal commands; keep in mind, you won’t want to forget the password you choose:
How to Set a Root Password
- While logged in as an administrator, open Terminal on your Mac.
- type the following command: sudo passwd root (The command “sudo” enables the user to run commands as a superuser and the command “passwd” is used to set a new password).
- You will likely be prompted for your password to authorize sudo.
- Next you should be prompted to enter a new password (for root). Enter the password (you won’t see any characters) and then press enter.
- Re-enter the password and press enter to confirm the change.
While using Terminal is generally much quicker, if you are more comfortable using your computer’s System Preferences to make this change please refer to Apple’s support article on How to enable the root user on your Mac or change your root password.
Generally speaking, Apple is very quick responding to security issues and they proved that they can work on a moment’s notice with their latest patch; however, this goes to show that no security is perfect. Even from the biggest names in the business, mistakes happen.






