PSA: Beware of Multiple Apple Password Reset Notifications
Toggle Dark Mode
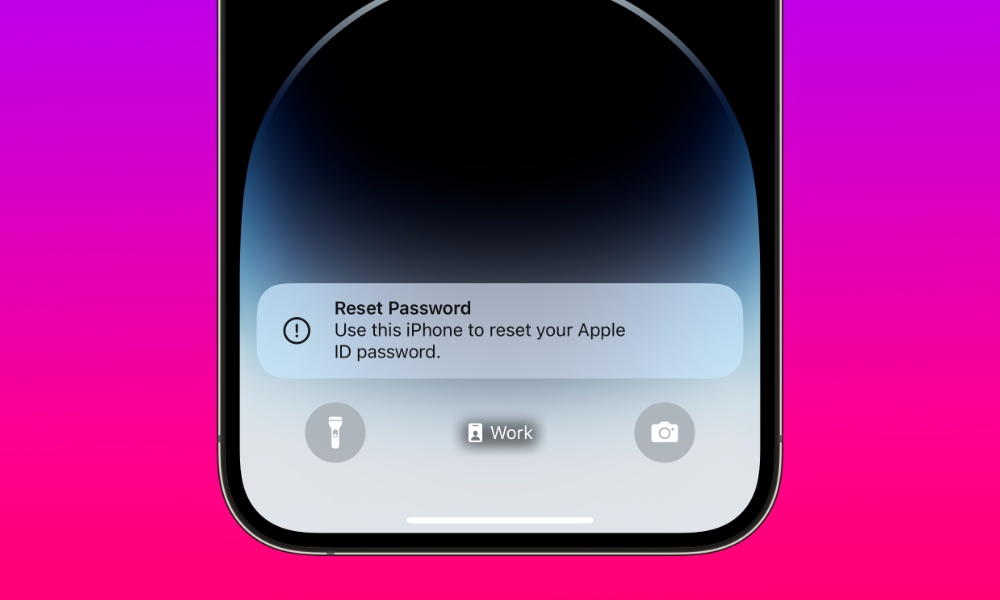
If you’re seeing multiple password reset notifications pop up on your iPhone, do NOT tap Allow under any circumstances. There’s a good chance someone is trying to hack into your Apple ID.
These are part of a targeted “spearphishing” attack that appears to be spreading. Cybercrooks are using a blunt form of social engineering to trick users into approving a password reset request.
As explained by Brian Krebs at KrebsOnSecurity, the attack, a type of “MFA Bombing” technique, exploits a weakness in Apple’s password reset feature. This weakness allows dozens of system-level prompts to inundate a user when a forgotten password reset request is made.
The attack was first reported on Twitter/X by entrepreneur Parth Patel. Patel provided a play-by-play on the social media network showing how he was targeted by the attack, which began with a series of password reset requests before being escalated to the more pointed social engineering tactics of a call from someone claiming to be from Apple Support.
Krebs notes that the first part of this attack relies on “MFA fatigue,” hoping that the seemingly endless stream of notifications will lead the victim to either make a mistake and fat-finger the wrong button or tap “Allow” just to make them stop coming.
All of my devices started blowing up, my watch, laptop and phone. It was like this system notification from Apple to approve [a reset of the account password], but I couldn’t do anything else with my phone. I had to go through and decline like 100-plus notifications.
Parth Patel, speaking with KrebsOnSecurity
Needless to say, approving such a prompt is a very bad idea. In this case, it would allow the attacker to reset your Apple ID password, thereby gaining access to everything associated with that, including all of your data in iCloud and even the locations of your Apple devices in Find My — and the ability to remotely wipe them all.
Patel persevered by continually declining these requests, after which the crooks decided it was time to take another tactic. Patel received a call on his iPhone that appeared to come from Apple Support — including a spoofed version of the valid 1-800 number. The person on the other end told him that his account was under attack and offered to “help” him fix the problem if he could simply verify a one-time code that they sent him via SMS.
Patel was suspicious enough not to fall for it. He asked the support rep to verify some information about him, but most of the data they provided was surprisingly accurate.
I pick up the phone and I’m super suspicious. So I ask them if they can verify some information about me, and after hearing some aggressive typing on his end he gives me all this information about me and it’s totally accurate.
Parth Patel, speaking with KrebsOnSecurity
Thankfully, there was one detail the scammers got wrong. They couldn’t supply Patel’s real name. Instead, they had an incorrect name for him that had been erroneously listed as an alias on his consumer profile at one point. While Patel likely wouldn’t have fallen for the call either way, that one incorrect piece of info was enough to confirm that it was a fake.
How to Protect Yourself
As annoying as this attack is, the good news is that it appears to be a highly targeted attack rather than a broader phishing campaign, and it’s easy to protect yourself if you exercise some diligence.
- Ensuring you continue to decline these requests by hitting Do Not Allow will keep your account secure.
- If you receive a call from someone claiming to be from Apple Support, hang up and call them back directly at the official number. It’s trivially easy to spoof a caller ID number for anybody who knows how, so don’t ever trust the number you see on your phone when answering an incoming call. Further, Apple has repeatedly stated that they will never initiate an unsolicited outbound call to a customer.
- Ensure your Apple account is secured with two-factor authentication and that you’ve set up a recovery key. While an Apple support rep told one person who fell prey to this attack that doing so would stop the reset requests, that’s not the case. However, it does help to further harden your account against such things. For example, tapping “Allow” in such a configuration will prompt the device you’re interacting with, such as your iPhone, to request the password change be made there.
- Consider using a different phone number or email address for your Apple ID. These attacks can only be initiated by someone with this information available, so if you use a VoIP number or an email alias only you know, it’s much harder for an attacker to identify your Apple ID.
What’s most frustrating is that if you do become a victim of this attack, there seems to be no way to make the password reset requests go away unless the attacker gets bored and gives up. Krebs cites several other folks he spoke with who had also been targeted by these attacks. A hedge fund owner named Chris went so far as to change all his passwords and even buy a new iPhone and set up a new iCloud account with a brand new email address. Despite this, the alerts continued on his new iPhone before he had even left the Apple Store, suggesting that it was somehow tied to his phone number.
Chris said he then proceeded to get even more system alerts on his new iPhone and iCloud account — all the while still sitting at the local Apple Genius Bar.
KrebsOnSecurity
This is where using a different phone number can help, but as Krebs notes, this may cause problems with using your real phone number with iMessage and Facetime.







