Did the US Government Leak iPhone Hacking Tools? Why You Should Keep Your iPhone Updated
Toggle Dark Mode
If you don’t keep your iPhone updated to the latest version of iOS you’re leaving it open to being violated by hackers. A recent revelation shows that iPhones running an outdated version of iOS can have as many as 23 security holes that can be exploited using a sophisticated toolkit that is now available to the bad actors of the world.
Law enforcement agencies and governments around the globe have long used hardware and software device cracking solutions to get around the iPhone’s security and privacy measures. Now, Wired reports that the bad actors of the world are buying an exploit tool that may have originally been created by none other than the United States government.
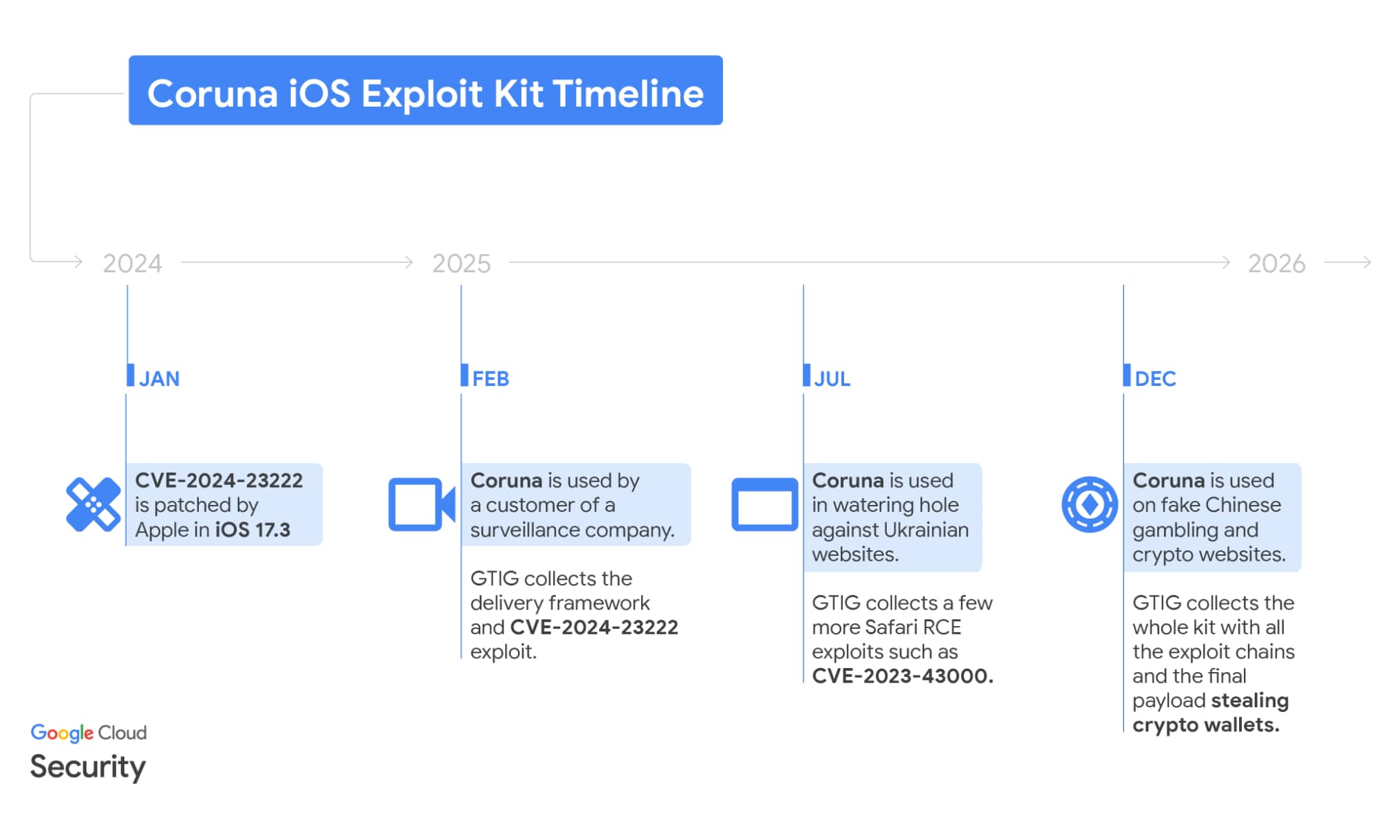
The report details information originally shared by Google’s Threat Intelligence Group and iVerify that explains how bad guys are using an exploit toolkit known as “Coruna” that has spread widely around the globe. Meanwhile, iVerify has traced the toolkit’s origins back to the US government.
The exploit toolkit reportedly contains five hacking techniques that utilize 23 vulnerabilities found in old versions of iOS. Specifically, iPhones that are still running iOS 13 (released in September 2019) to iOS 17.2.1 (released in December 2023) can be infected by simply visiting a webpage.
Reports like these are the reason why Apple (and iDrop News) strongly advise iPhone users update immediately to the latest iOS release available for their devices. That’s iOS 26.3 if your iPhone is capable of running it, but analysts note that fewer than 75% of iPhones capable of running iOS 26 have been updated. The good news is that Apple also continues to release critical security fixes for older iOS versions — iOS 18.7.5, iOS 16.7.14, and iOS 15.8.6 as of this writing — but those are primarily targeted at devices that can’t be updated to iOS 26.
Each of these updates includes all the previous patches that Apple has released to safeguard against attacks like these, but it’s important to remember that new exploits are being discovered every day. Just because the latest patches have neutralized these latest tools doesn’t mean there aren’t already newer versions of them that haven’t leaked out, and it’s a safe bet there will be plenty more where these came from.
What Does Coruna Do, And How Does It Spread?
Coruna targets vulnerabilities found in WebKit, which is the engine used for the Safari browser. However, while there are no confirmed techniques in the toolkit for Chrome, Apple requires that all mobile browsers on the iPhone use the same WebKit engine, which means they all share the same vulnerability.
Notably, the toolkit also checks if the device is in Lockdown Mode or in a private browsing session, and doesn’t attempt to hack the device in these cases.
While that means private browsing can be used to mitigate this specific threat until you can update, but you probably won’t want to turn on Lockdown Mode, as it’s a highly restrictive mode to be used by journalists and other high-profile individuals who potential targets for mercenary-grade spyware like Pegasus. For everyday users, the latest iOS patches will be sufficient to protect your device against this toolkit and many other threats that couldn’t care less about private browsing.
If iVerify’s report is correct, the US government developed a set of sophisticated exploit toolkits for use against iPhone users prior to 2025. The code’s similar use of frameworks, the level of sophistication, and code writers speaking English all indicated to iVerify that the US was behind the toolkit.
“It’s highly sophisticated, took millions of dollars to develop, and it bears the hallmarks of other modules that have been publicly attributed to the US government,” iVerify cofounder Rocky Cole said in a statement. “This is the first example we’ve seen of very likely US government tools— based on what the code is telling us— spinning out of control and being used by both our adversaries and cybercriminal groups.”
iVerify indicates that approximately 42,000 devices may already have been hacked with a specific version of Coruna being used in a Chinese-language cybersecurity attack. An unknown number of Ukrainians have been infected by a Russian espionage operation.
As can be expected with toolkits like this, the code was leaked and the US government lost control of the tool, which ended up on the black market. The original buyer of the toolkit then sold a manipulated version of the kit, then the next buyer added their own secret sauce, and on and on and on, creating multiple variants designed to perform different evil tasks.
There have been other theories about how Coruna originated, as iVerify’s Rocky Cole indicated that the toolkit could have had origins in components that Russia had said were used by US hackers. However, as pointed out by AppleInsider, it appears to have been a well-funded development process.
Toolkits like Coruna are not only a good argument for keeping your iPhone updated to the latest version of iOS, but are also a good advertisement for why Apple should never give into law enforcement or governments that are in search of “backdoor” access to the end-to-end encrypted data stored on your iPhone. Apple CEO Tim Cook once likened such a backdoor to “the software equivalent of cancer,” noting that it would not only violate Apple users’ privacy but could also be leaked to bad actors, much like the Coruna toolkit, to be used against Apple device owners.