Apple Killed Encrypted iCloud Backups After Being Pressured by the FBI
 AppleInsider
AppleInsider
Toggle Dark Mode
Apple has reportedly ditched plans to bring end-to-end encryption to iCloud backups after receiving some pressure from the FBI, Reuters reported on Tuesday.
The Cupertino tech giant had been working on encrypted iCloud backups for more than two years, several sources familiar with the matter told Reuters. One of those insiders said that “legal killed (the feature), for reasons you can imagine.”
Apparently, the FBI had raised concerns that the iCloud backup encryption would hinder criminal investigations. That pushback lead to the abandonment of the feature about two years ago, presumably sometime in 2018.
End-to-End Encryption
End-to-end encryption refers to systems that protect data by ensuring only the sender and recipient can read it. In the case of iCloud backups, this would mean that the data would be encrypted with a key not stored on Apple’s servers.
That means that if someone hacked those servers, or if Apple handed the backups over to authorities, the data within those backups would look like gibberish rather than anything discernible.
But currently, Apple stores iCloud backups with decryption keys on its servers. That means that if a law enforcement or government entity produced a subpoena for that data, Apple would give it up.
This does have some worrying implications for Apple’s other end-to-end encrypted services. Take iMessage, for example. A government entity wouldn’t be able to read the conversations of your texts. But if your iMessages are stored in iCloud, they could access them that way.
Apple actually end-to-end encrypts many of its services. But other services, like email and photos, are not encrypted. And if a user uses iCloud backup, it pretty much negates the benefits that you’d get from end-to-end encrypted iMessages.
Apple and Government Pressure
Apple has had an interesting relationship with various government and law enforcement entities over the years.
On one hand, the company has publicly refused to comply with the creation of backdoors into its hardware and software systems. It also frequently patches security vulnerabilities used by police hacking tools.
But on the flip side, Apple does comply with government requests for data. A recent example being the Penascola shooter situation. After receiving flack from higher-ups in the Trump Administration, Apple said that it actually handed over tons of iCloud data to authorities.
This Reuters report is just the latest evidence that Apple and the government may be closer than you think.
Back in 2016, for example, The New York Times reported that Apple was developing more end-to-end encryption features. But rumors about those features fizzled out completely. That gives a timeline that lines up almost perfectly with the apparent FBI pressure in 2018.
What Users Could Do
For most users, this is more of a philosophical than a practical debate. But there are, of course, users with much more sensitive security and privacy needs.
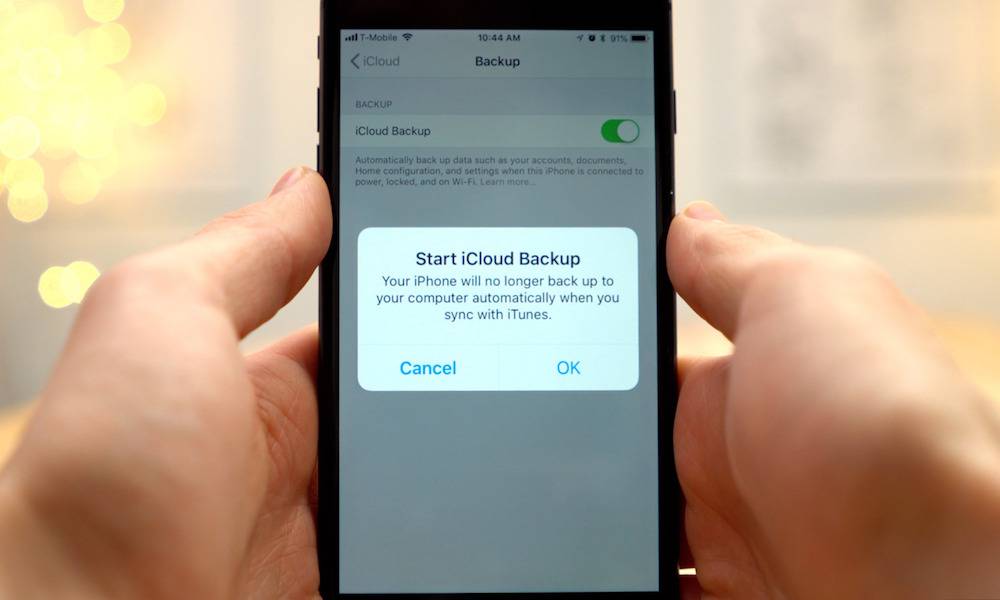
Looking at it currently, it seems the only way to overcome this potential risk is to skip using iCloud and rely on encrypted iTunes backups.






