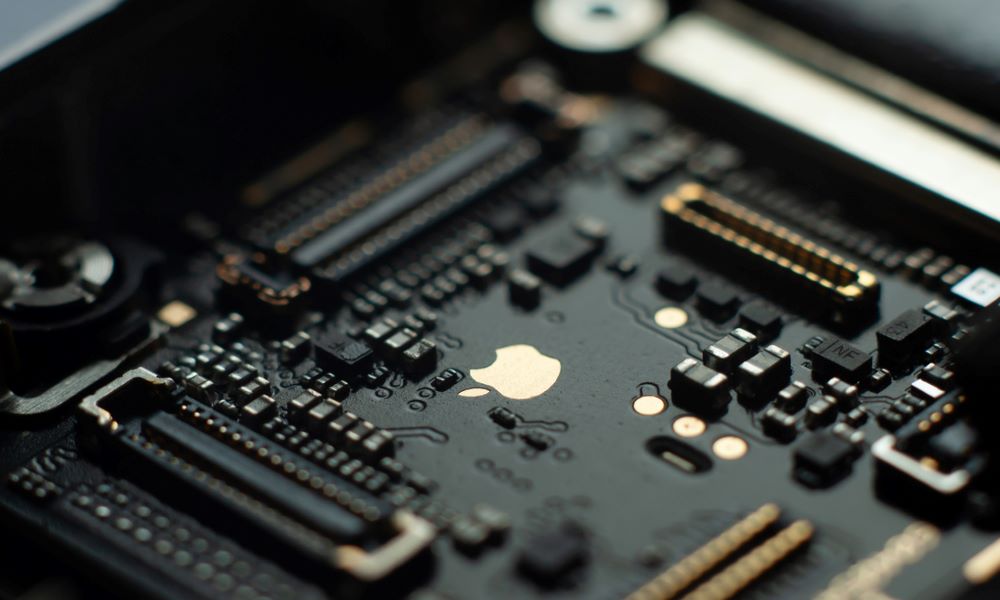
Apple’s T2 Chipset May Have Unpatchable Security Flaw
Toggle Dark Mode
Apple added the T2 co-processor to its newer Mac models as a security measure. The chipset handles encrypted storage, provides a secure boot environment, and more. Despite its focus on security, this chipset may not be as safe as we assume. According to a team of jailbreakers who discovered the flaw, the SepOS software that controls the T2 chipset has an unpatchable security flaw. And it could be serious, claims security researcher Neil Hofmans. Continue reading to learn why the T2 chipset is problematic.
The vulnerability harkens back to the AA10 chipset, which Apple first used in the iPhone 7 and 7 Plus. The T2 chipset is based on Apple’s A10 processor, which is vulnerable to the checkm8 jailbreak exploit. This same vulnerability that lets hackers access the A10 is also present in the SepOS on the T2.
In the T2 chipset, the vulnerability can intercept the boot process of the T2 operating system providing access to the underlying hardware. Typically, the chipset would exit the process with a fatal error if it detected such an intrusion. This vulnerability, though, lets hackers bypass this security check and gain access to the T2 chip.
Hackers Could Get Control
Once a hacker has gained access to the T2 chip, they have nearly full control over the chipset. The one thing a hacker could not do is decrypt the files on the hard drive stored using Apple’s built-in FileVault 2 encryption. This is just a minor hurdle. They could hijack the keyboard and install a keylogger that steals passwords, including the password used to decrypt the files on the hard drive.
SepOS is installed on the T2’s read-only memory (ROM), which cannot be altered. This means Apple cannot release an update to patch this security flaw. Apple was made aware of this vulnerability but reportedly has not responded yet either to the security researchers or the public.
Not All Bad
It’s not all bad news, though. To access this vulnerability, a hacker can only access it through an attached component like a USB-C cable. For the average consumer, this is not an issue. They always know where their computer is and what is being connected to it. Companies that routinely use peripherals and have a fleet of computers to tracker may be more vulnerable.
This also may be a non-concern for future MacBooks, which are switching over to an ARM-based architecture. It is not yet known, but it’s possible that Apple’s ARM-based Macs may not be affected by this vulnerability.
[The information provided in this article has NOT been confirmed by Apple and may be speculation. Provided details may not be factual. Take all rumors, tech or otherwise, with a grain of salt.]






