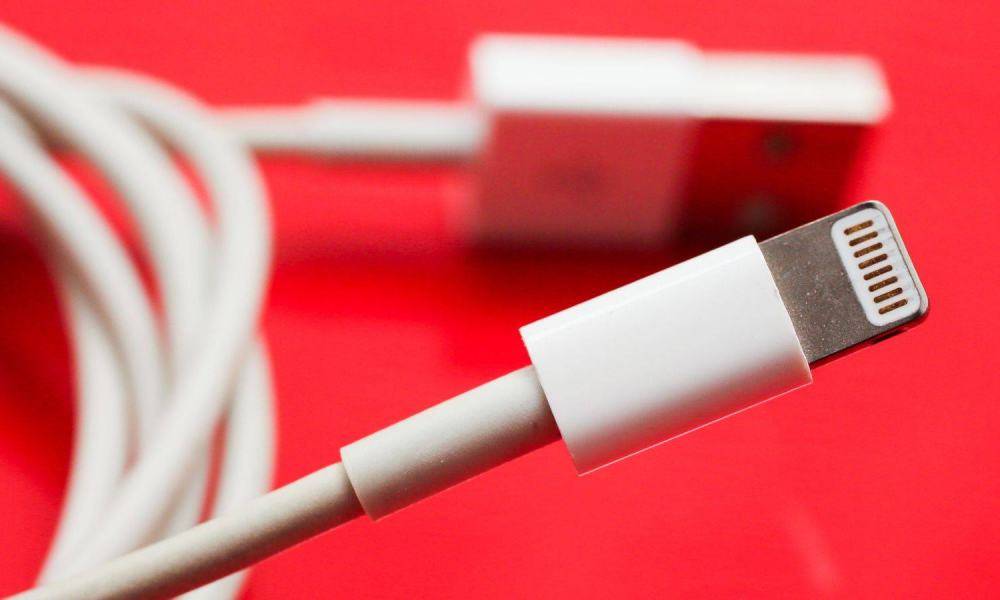
Your Lightning Cable Could Be Letting Hackers into Your Mac
 Credit: CNET / Sarah Tew
Credit: CNET / Sarah Tew
Toggle Dark Mode
Your innocuous looking Lightning cable could be hiding a secret chip that would allow hackers to remotely infiltrate your computer, underscoring the need to always purchase legitimate Lightning cables from trusted sources.
A security researcher at this year’s Def Con, known only as MG, demonstrated how a ordinary iPhone Lightning to USB cable can be rigged with an embedded chip that would allow a nearby hacker to take full control of a Mac or Windows PC without giving any indication to the user that they’ve been compromised.
It looks like a legitimate cable and works just like one. Not even your computer will notice a difference. Until I, as an attacker, wirelessly take control of the cable.
M.G., security researcher
Known as the O.MG Cable, it not only looks like an ordinary Lightning cable, but functions the same in every other way as well. As Motherboard reports, plugging the cable in gives absolutely no sign that anything is amiss, with it charging a connected iPhone, iPad, or iPod and syncing data with iTunes in exactly the same way as a normal Lightning cable. Embedded within the cable, however, is a Wi-Fi chip that allows a hacker to remotely access the USB port that the cable is plugged into and run commands just as if they were sitting in front of the screen of the target computer.
While MG chose to use an Apple Lightning cable as his proof-of-concept, there’s nothing special about Lightning cables in this regard, and the technique can be adapted to any USB cable; MG notes that Apple’s cable is just the most difficult one to implant the chip in, so his idea was that if he could do it to a Lightning cable, he can do it to any cable.
How It Works
The technique demonstrated by MG required the attacker to be wIthin about 300 feet of the target in order to connect to the Wi-Fi network being broadcast by the cable’s embedded chip, however MG notes that it would be easily possible to program the chip to connect to any nearby Wi-Fi networks, thereby allowing the user’s computer to be compromised from anywhere in the world.
Although the chip allows direct keyboard access to the victim’s computer — presumably simply by emulating a USB keyboard — MG also demonstrated how it can be pre-installed with various scripts that provide automated attacks to run on the target machine, ranging from stealing data to redirecting the user to fake websites for phishing purposes. The implant can also be remotely “killed” once the hacker is done with it, hiding much of the evidence of its existence.
Should You Be Worried?
As with most of these types of security research projects, the goal is to raise awareness of the possible issue, rather than to market an actual tool for malicious hackers. However, MG was also able to build these cables in his kitchen without any particularly specialized tools, although each one took about four hours to make, and while he is selling the O.MG cables, he’s seemingly only offering them to other legit security researchers.
However, if MG can do this, it stands to reason that other hackers with less altruistic motives could do likewise, and it’s entirely possible that it’s already been done. One possible attack vector suggested by MG would be to either swap the malicious cable for a user’s legitimate cable without them knowing, or to even give the malicious cable to the target as a gift, as they could easily be packaged to look like an official Apple cable.
At this point there doesn’t appear to be any known defence against this attack, although we’d suspect that Apple will soon take steps in future releases of macOS to tighten up security on the USB port in much the same way that it has for the iPhone’s Lightning port.
Until then, however, this is a good reminder that things aren’t always as they seem in the world of technology, and another reason to always purchase Lightning cables from known and trusted sources. It’s very unlikely that Apple Lightning cables found on the shelves of an Apple Store will be compromised, but you may not be able to be completely certain with cables purchased from other sources.






