This Is Why You Should Update to iOS 13.3 as Soon as Possible
Toggle Dark Mode
Apple has fixed a critical bug in iOS 13 that could let anyone temporarily overwhelm and freeze up an iPhone using AirDrop.
The bug was first discovered by engineer and security researcher Kishan Bagaria, TechCrunch reported. Bagaria found that AirDrop let him repeatedly send files to any device able to accept them within range.
By default, iOS blocks the display when an AirDrop file is received until it’s either accepted or rejected. But AirDrop also doesn’t limit the number of files that someone can send.
Using an AirDrop tool call OpenDrop, Bagaria found that he could easily overwhelm an iPhone by sending large files over and over again, effectively rendering the device stuck in a loop. He could even target pretty much any device within wireless range.
He dubbed the technique “AirDoS.” If you’re familiar with DDoS attacks, you know that the “DoS” stands for “denial-of-service.” In short, it means that a user pretty much loses access to their device.
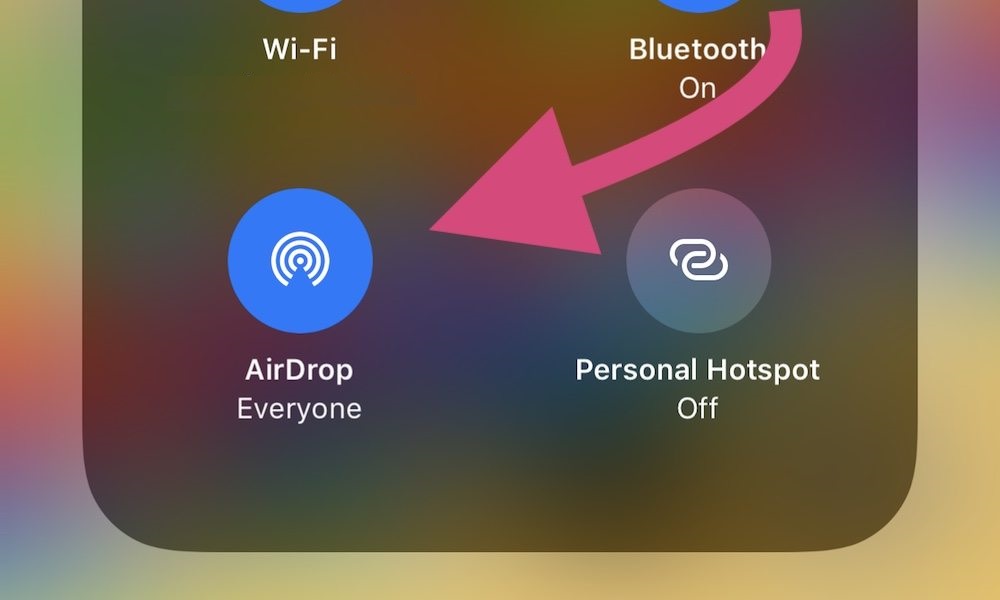
Of course, only iPhones with their AirDrop settings set to “Everyone” are really at risk of this attack. Luckily, that isn’t the default setting out of the box.
As mentioned earlier, Apple has addressed the bug in iOS 13.3 by adding a limit to the number of send requests that can be sent in a short period of time. But if you haven’t updated yet, then your device is vulnerable. That’s even more of a concern since the details of the attack are now public.
If you can’t update immediately, then we recommend going into:
- Settings.
- General.
- AirDrop.
- Set it to Contacts Only.
On the other hand, if someone does manage to trigger an “AirDoS attack” on your device, there isn’t really an easy way to mitigate it. Turning off Bluetooth works, but that isn’t an easy feat since the AirDrop pop-ups are incredibly persistent.
But Bagaria notes that getting out of Bluetooth range will stop them, so “simply run away.”
Because this wasn’t strictly a security vulnerability, Apple hasn’t provided a CVE score to the bug. Instead, it publicly acknowledged it (and Bulgaria’s work) in a section of its security updates page.






