Researchers Have Figured Out How to Send Secret Messages via the Find My Network
 Vladimka Production / Shutterstock
Vladimka Production / Shutterstock
Toggle Dark Mode
Ever since Apple first took the wraps off its Find My network and AirTags last month, security researchers have been poking at the various technologies to find out how they work and if there are any security risks or vulnerabilities that could be of concern.
So far, however, the good news is that they haven’t found anything significant, although they’ve certainly unearthed some interesting tidbits. For example, last week one researcher figured out how to reprogram an AirTag, although so far, their efforts don’t seem to have accomplished much more than changing the URL that’s transmitted over NFC.
Now, another security researcher has taken aim at Apple’s underlying Find My network instead, discovering that it’s possible to send messages and other small bits of arbitrary data into it using any nearby Apple device — without the owner’s knowledge or consent.
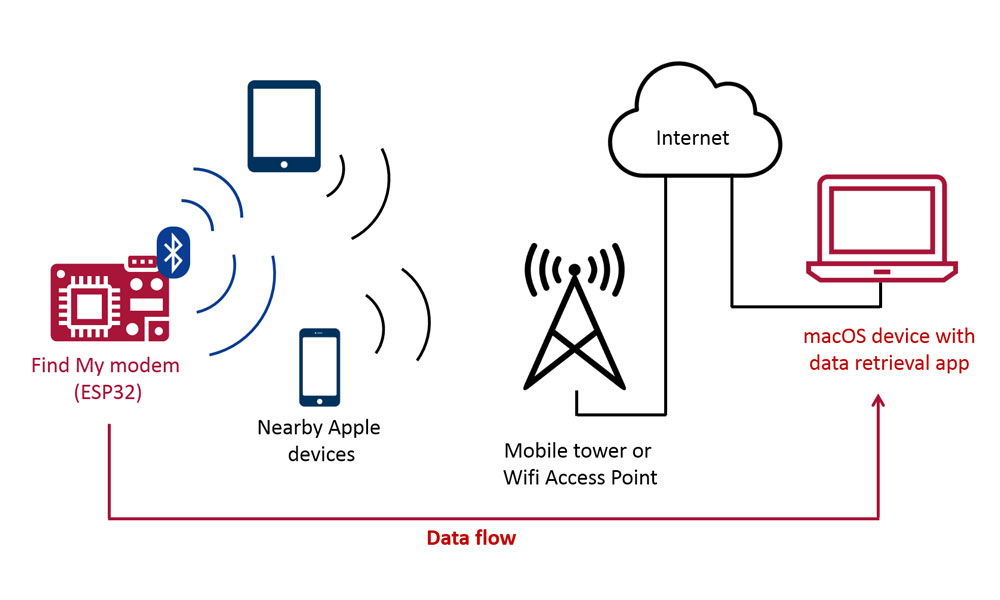
According to Positive Security, the trick works by essentially emulating an AirTag or other Find My network-compatible item to broadcast information over a Bluetooth LE channel that will be picked up by any nearby iPhone, iPad, or Mac, and passed into Apple’s Find My network.
The security researcher behind the discovery, Fabian Bräunlein, suggests that there are practical and non-sinister uses for such a capability, while also adding that there’s likely nothing Apple can do to prevent it because of how the Find My network is designed with “zero-knowledge” privacy of all the data that passes through it.
While I was mostly just curious about whether it would be possible, I would imagine the most common use case to be uploading sensor readings or any data from IoT devices without a broadband modem, SIM card, data plan or Wifi connectivity.
Fabian Bräunlein, Positive Security
That said, Bräunlein does imagine a more nefarious use for the feature, although it’s still not something that every AirTag and Find My user would need to be concerned with. It’s more about using iPhones as unwitting accomplices in a scenario that sounds like something out of a John le Carré novel.
In the world of high-security networks, where combining lasers and scanners seems to be a noteworthy technique to bridge the airgap, the visitor’s Apple devices might also become feasible intermediaries to exfiltrate data from certain airgapped systems or Faraday caged rooms.
Fabian Bräunlein, Positive Security
In either case, however, the key would be to use any nearby iPhone as a silent intermediary to send small packets of data to another destination, and the design of the Find My network would make for a very secure way to do this.
Can Apple Block These?
By its very nature, this would be a misuse of the Find My network, but as Bräunlein explains, it would actually be very hard for Apple to prevent these messages from being exchanged, as its own security, encryption, and privacy features would essentially be working against it.
In fact, even though Apple only just opened up its Find My network to third parties, it actually goes back to 2019. It was first introduced in iOS 13 as an improvement to Find My iPhone that would allow your iPhone, iPad, or Mac to be located by other Apple devices — even if they weren’t online.
While Find My iPhone has been around for over a decade, it always relied on a cellular or Wi-Fi connection so that it could report its own location. When Apple expanded it to the iPad, iPod touch, and Mac, it was considerably less useful, as those devices could only report while on a Wi-Fi connection.
To address this problem, Apple laid the foundations of what would ultimately become the Find My network we know today, allowing iPhones, iPads, and Macs to be located in exactly the same way that you can now also locate AirTags and other Find My compatible items.
So, even though the Find My network has produced some more interest among security researchers with the advent of AirTags, it actually works much the same way as it did two years ago — and it was designed with some remarkable privacy and security features.
Chief among these is the fact that every piece of data on the Find My network is encrypted in such a way that even Apple can’t read it. This means that Apple cannot track the location of your AirTags, your VanMoof eBike, or even your iPhone, iPad, or Mac.
This is why you need two Apple devices to use the Find My network — and also why Find My Items doesn’t work on the web. To find your items, you need the matching key to pull them out of the meaningless expanse of encrypted device IDs. When you open Find My on your iPhone, iPad, or Mac, it sends an encrypted lookup request to Apple to retrieve the data that matches your AirTag or other Find My item, and that data is downloaded and decrypted locally on your device.
At the time, cryptographers and security researchers applauded the brilliance of this design, but it turns out it’s also a double-edged sword.
You see, this also means that Apple doesn’t know anything at all about the data that’s passing through its network. It just sees random encrypted blobs of data. Apple assumes that these are just the identities of billions of AirTags and other Find My devices floating around the world, but as Bräunlein has discovered, these data packets can contain anything.
Apple designed the system on the principle of data economy. They cannot read unencrypted locations and do not know which public keys belong to your AirTag, or even which public key a certain encrypted location report belongs to (as they only receive the public key’s SHA256 hash).
Fabian Bräunlein, Positive Security
Further, several of the methods that Bräunlein envisions Apple potentially using to prevent this would require devices considerably more sophisticated and powerful than AirTags. For example, Apple doesn’t require AirTags or other Find My devices to actually authenticate to the Find My network. This makes it possible to spoof “many thousands of non-existing AirTags” by basically making up IDs, which can then be used to encode and transmit data onto the network.
Should You Be Worried?
There’s no reason to believe right now that any of this poses a risk to everyday iPhone users. Even if this technique became widespread, in the very least your iPhone would simply be used as a passthrough device to send these small messages.
More importantly, however, nothing in this technique provides any way of accessing your Find My devices. In fact, it’s the extremely strong security and privacy of the Find My network that makes this technique possible in the first place.
It’s also important to note that Bräunlein’s technique can only send minimal amounts of data. Remember that the Find My network is only intended to transmit the IDs of AirTags and other items, which are extremely small bits of data. While a message could easily be broken into multiple packets, the amount of back-and-forth traffic would seem to make it impractical for sending anything other than relatively short messages and other small amounts of data.
This means that even if your iPhone became an unwilling participant in this stealth network, there’d be little risk of you burning through your data cap or taking a serious hit on battery life.
Either way, at this point the technique remains little more than a proof of concept. Bräunlein has published the code on Github for anybody who wants to play with it, although it requires specialized hardware in the form of an ESP32 microcontroller with custom firmware to inject the messages into the Find My network in the first place, so it’s not something that most users will be able to try at home.