Massive Vulnerability Discovered in Third-Party Security Tools for Mac

guteksk7 / Shutterstock
Toggle Dark Mode
Security researchers have discovered a massive vulnerability in third-party macOS security tools that went unnoticed for nearly 11 years.
Impacted security tools include those made to detect software with suspicious developer signatures. But researchers found that there was an extremely easy way to trick those tools into thinking a malicious app was actually signed by Apple, Ars Technica reported on Tuesday.
That method was so “trivial,” in fact, that basically “any hacker” could pass off a malware-laden app as official Apple software, researchers told Ars Technica.
And as mentioned earlier, the exploit existed within Apple’s documentation for a little over a decade — seemingly without security researchers or Apple’s own engineers noticing it.
How It Works
The exploit basically zeroes in on digital key signatures, Apple’s way of informing users that an app came from a legitimate developer or an otherwise trusted source.
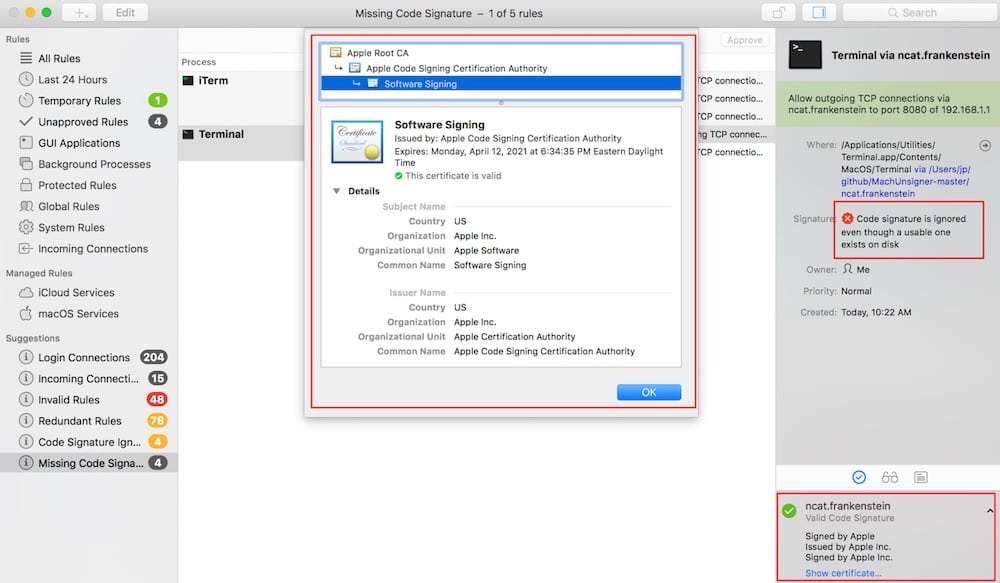
Image via Okta
As mentioned above, the exploit basically lets anyone insert malicious code into software that appeared to be “signed” by Apple. That could have allowed malicious apps to bypass security tools that barred software by untested developers from being installed.
It impacted third-party security tools from the likes of Facebook, Google Santa, VirusTotal, Carbon Black, Yelp, OSXCollector, and others.
Unlike similar Windows-based exploits that rely on stealing real signatures from legitimate developers, the Apple exploit didn’t require any theft.
The vulnerability was first spotted by Joshua Pitts, a senior penetration tester at security firm Okta. Pitts said the method was “really easy” to take advantage of.
It is not, however, a bug on Apple’s part. Rather, security researcher and developer Patrick Wardle told Ars Technica that it was simply unclear documentation that allowed malicious actors to use the API incorrectly.
If you’re particularly savvy, you can read more about the technical details of the vulnerability on Okta’s site.
How It Could Affect You
One of the chief concerns centers on how easy the exploit was to use. And that’s especially worrying in light of reports that fraudulent app signing is much more widespread than originally thought.
“This really scared the bejeezus out of me, so we went right to disclosure mode,” Pitts told Ars Technica.
Pitts discovered the vulnerability in February and informed both Apple and third-party security developers about it soon thereafter.
According to Okta’s disclosure timeline, Pitts sent a report to Apple, who responded a few days later. Okta reports that Apple said the issue doesn’t seem to be one that should be directly addressed.
Pitts added that the vulnerability did not affect security tools that are built-in into macOS or OS X. Because of that, users should only be concerned if they’re heavily relying on third-party apps for their security needs.
Luckily, the exploit seems to have been addressed by the third-party manufacturers — and Apple has made the related documentation much more clear. Just keep your security tools and software up-to-date, and you should be fine.






