How Amazon CEO Jeff Bezos’ iPhone X Was Hacked and Exploited
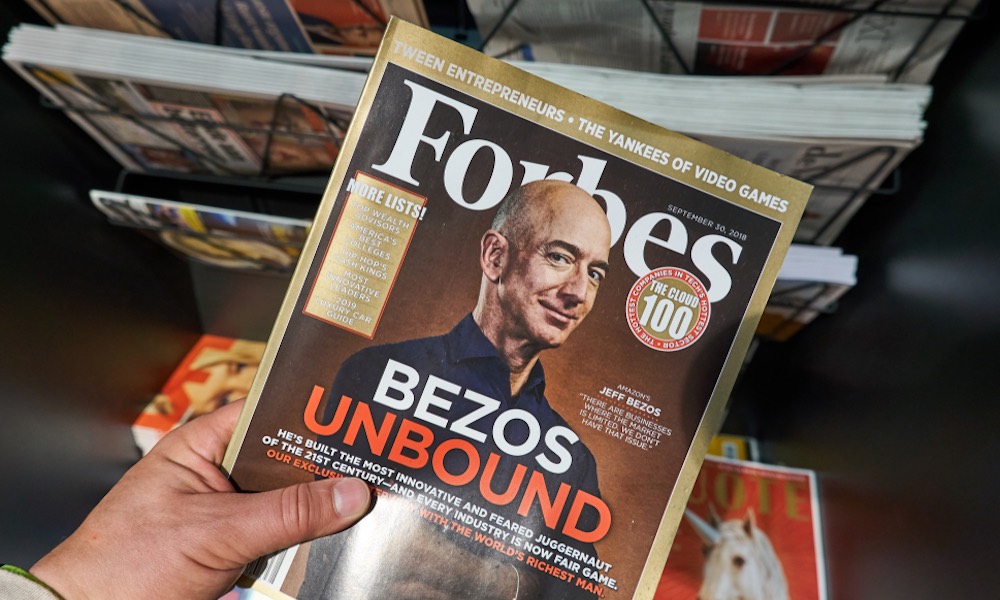 dennizn / Shutterstock
dennizn / Shutterstock
Toggle Dark Mode
Nearly two years ago, Jeff Bezos’ iPhone X was hacked. Since 2019, the Amazon CEO has been on a mission to figure out who did it and how. The study is, of course, tied up with the alleged blackmail and extortion situation from early 2019. But one an interesting and overlooked part of the saga is not that Bezos’ phone was targeted and exploited, but how.
How Jeff Bezos’ iPhone Was Hacked
In the wake of the apparent hacking, Bezos hired cybersecurity experts specializing in forensic analysis. The results of that investigation showed “medium to high confidence” that Bezos’ iPhone X was hacked.
That may come as a surprise to users familiar with iOS’s reputation as a secure system. But, of course, there’s no such thing as being fully “hack-proof.”
Still, the forensic analysis appears to show that the attackers took advantage of a security vulnerability in WhatsApp to install malware on Bezos’ iPhone X, according to a new report by The New York Times.
On May 1, 2018, Bezos received a WhatsApp message from an account that belonged to Saudi crown prince Mohammed bin Salman. That message contained a 4.4MB video file of Saudi and Swedish flags, as well as some Arabic text.
But it appears that a tiny bit of code hidden within that video successfully exploited a vulnerability that allowed malware to be installed on the iPhone X. After receiving the video, the iPhone began sending unusually large amounts of data. Later reporting suggests that that data included personal and sensitive information.
If there’s a silver lining to the story, it’s that the malware used was highly advanced. In fact, it was likely tailor-made by an expert cybersecurity firm displaying a level of sophistication beyond the average cybercriminal.
And, of course, Facebook — who owns WhatsApp — has since fixed the vulnerability that the malware likely exploited.
What This Means for You
iPhones, like anything else connected to the internet, can be hacked. Luckily, the average iPhone user has different security needs than the CEO of Amazon.
With enough time and resources, there’s a good chance that a focused attacker can hack your device. But unless you’re a public figure, there may not be much motivation for a determined hacker to specifically target you.
Still, there’s currently a deluge of iPhone vulnerabilities out there. And even if you’re an average iPhone user, you may still be a target for cybercriminals. With that in mind, here are a few simple tips to help keep you safe.
- Avoid clicking on links, files or websites that you’re unsure about — particularly from contacts you don’t know.
- Be suspicious of any person, site or app requesting personal information like financial data or passwords.
- Keep iOS and all of your third-party apps as up-to-date as possible.
- Don’t install configuration profiles from a third-party on your device, it’s one of the easiest ways for an attacker to get malware on it.
- Use two-factor authentication and a password manager to keep your important accounts secure just in case you do get hacked.






