Here’s Why It’s Dangerous to Pirate Mac Apps
 Foxartbox / Shutterstock
Foxartbox / Shutterstock
Toggle Dark Mode
For iPhone and iPad users, the App Store is the only legitimate game in town for getting apps onto your device, and although the Mac still allows apps to be installed old-school, many developers now push their apps through the Mac App Store for the increased safety, security, and simplicity, however, this hasn’t stopped piracy in various forms, even for those apps on the App Store.
For instance, last year we saw software pirates abusing enterprise developer certificates to create underground websites for apps, and even before that, the jailbreak has long provided a platform for getting pirated apps on iOS devices.
However, since Mac apps can still be installed independently of the Mac App Store, software pirates haven’t had to resort to such complex means to distribute bootlegged Mac apps, but even leaving aside the obvious ethical issues if you’re looking for a way around paying for your Mac apps, here’s another cautionary tale that should make you think twice.
‘EvilQuest’
Even if you don’t buy all of your apps from the Mac App Store — and let’s face it, some apps just aren’t available that way anyway — when you purchase an app from a legitimate developer’s website, you know you’ll be getting a clean version of the app.
This is something you can’t be the least bit confident in when getting apps from other, more questionable sources, however, many Mac users are lulled into a false sense of security based on the old myth that “Macs don’t get viruses.”
While it’s true that the more secure architecture of macOS makes it less prone to viruses, especially compared to the Windows PCs of yesteryear, that by no mean makes your Mac immune to viruses, and this is especially true if you’re deliberately downloading a virus onto your computer (whether you know it or not).
In short, macOS can only go so far in protecting users from their own stupidity, and applications are still applications, so if you download a program that contains bad code and explicitly run it, macOS will happily follow your instructions, even if that means wiping out every file in your Documents folder.
The latest case in point of this is new “ransomware” that’s not being discovered latched onto seemingly-legit, albeit pirated, Mac apps.
As reported by Malwarebytes, the new ransomware, which has been dubbed “EvilQuest” was found in a pirate copy of the Little Snitch app that’s been making the rounds on Russian forums and torrents. The download comes in a PKG file that actually contains a valid copy of Little Snitch but also bakes in another script that runs after users install the app that dumps ransomware onto your Mac.
Postinstall scripts normally run to clean up files after the installation of an app, but of course they can do a lot more, since they’re ultimately just scripts that run on your Mac. Notably, the actual legitimately purchased version of Little Snitch doesn’t come as a package file at all.
Malwarebytes has a more in-depth analysis for those interested in the gory technical details of how this all gets installed on your Mac, but the main effect of this particularly nasty little piece of ransomware is to start encrypting whatever files it can get its hands on, from your documents to system files and things like the macOS system Keychain.
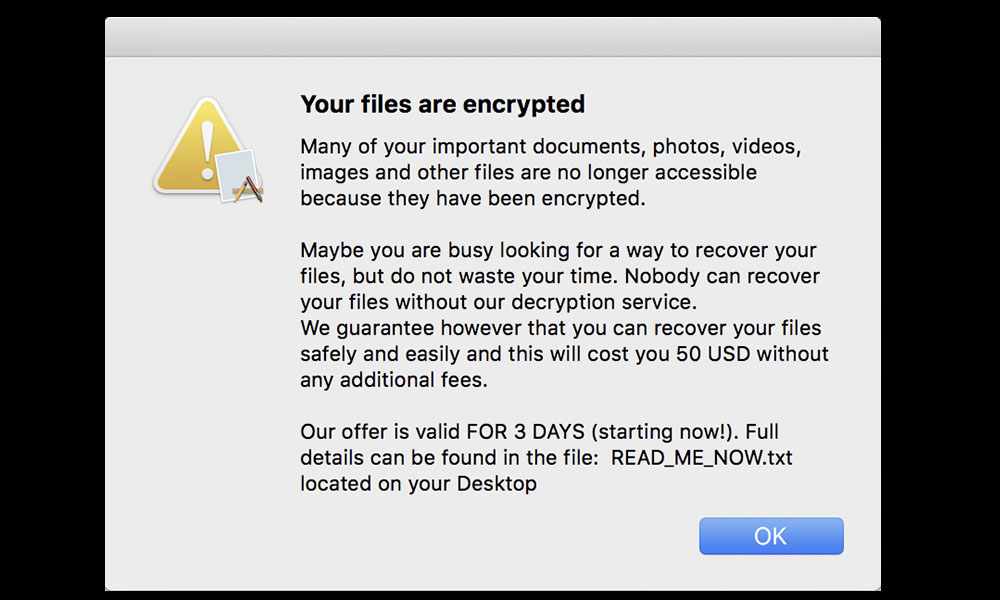
While it apparently takes a bit of time before the ransomware starts doing its thing, once it does users are shown a pop-up telling them that their files are now encrypted, and presenting a limited time offer for a “decryption service” that can be used to unlock your files.
This of course is where the “ransom” in “ransomware” comes in, since what EvilQuest does it to effectively hold all of your files, and in fact potentially your entire system, hostage, and due to the nature of encryption, there really is no simple way to get back at your data unless of course you have backups from before your computer became infected.
Synchronized cloud storage won’t help you here either, since even if you’re using iCloud, Google Drive, Dropbox, or another similar service, as your files are encrypted, the encrypted versions will be uploaded to your cloud storage service, overwriting the unencrypted ones. If you have a cloud service that provides versioning or the ability to restore from older backups, you could get some of these back, but they’re ultimately no replacement for actual regular offline backups.
That said, Malwarebytes is still conducting further analysis, and suggests that it’s possible that the encryption used by EvilQuest could be easier to crack, but that’s far from a sure thing.
Unfortunately, once EvilQuest has begun encrypting your files, the only way to get rid of it is by formatting the entire disk and restoring from backup.
How to Avoid Malware on your Mac
To be fair, the secure architecture of macOS usually makes it difficult for most malware to gain a foothold without engaging in some pretty risky behaviour and specifically bypassing security controls that are normally designed to prevent this sort of thing.
For example, there’s the obvious matter of downloading pirated apps in the first place, although sometimes that’s not as obvious. For example, users who might never even think of visiting a Russian torrent site might be perfectly happy to install a copy of an app that a friend sends over to them, and you may not realize where this actually came from.
Unfortunately, as good as some of the protections in macOS are, too many users have been conditioned to just go right through them without giving them much thought. For example, when prompted to enter an administrator password to install an app, most users will just happily key it in almost from muscle-memory without stopping to ponder why the app they’re installing actually needs administrator privileges (and neither Apple nor app developers do as good as job as they should of explaining this).
That said, even the most diligent and security-conscious Mac users can still be tripped up sometimes, especially since flaws do occur in macOS from time to time that can be exploited by malware. While anti-malware software can certainly help, the best thing you can do to avoid these sorts of problems is to question everything that you choose to install — especially if it doesn’t come from the Mac App Store — and also keep regular backups, at least one of which should be on a hard drive that’s not normally connected to your Mac.