Personal Data of 31 Million Users Leaked from Popular Keyboard App
Toggle Dark Mode
Security researchers have discovered that personal data belonging to over 31 million users of a popular keyboard app was leaked online, according to a new report.
The massive leak was first discovered by the Kromtech Security Center, who found that they were able to access a database containing the sensitive information of 31,293,959 users of keyboard app Ai.Type. Reportedly, the app’s developers failed to secure the database’s server with a password, allowing anyone to easily access the user records.
What Information Was Leaked?
The sensitive information included a user’s full name, email address, SMS number, device name and model, mobile network name, and IMEI number, as well as a user’s precise location and city and country of residence. The database also seemed to contain information from a user’s public social media profiles, including their birthdates and their profile pictures.
All in all, Kromtech’s researchers were able to unearth about 577 gigabytes of user records. Reportedly, the database seemed to have contained mostly information on the app’s Android users — though reports are conflicting.
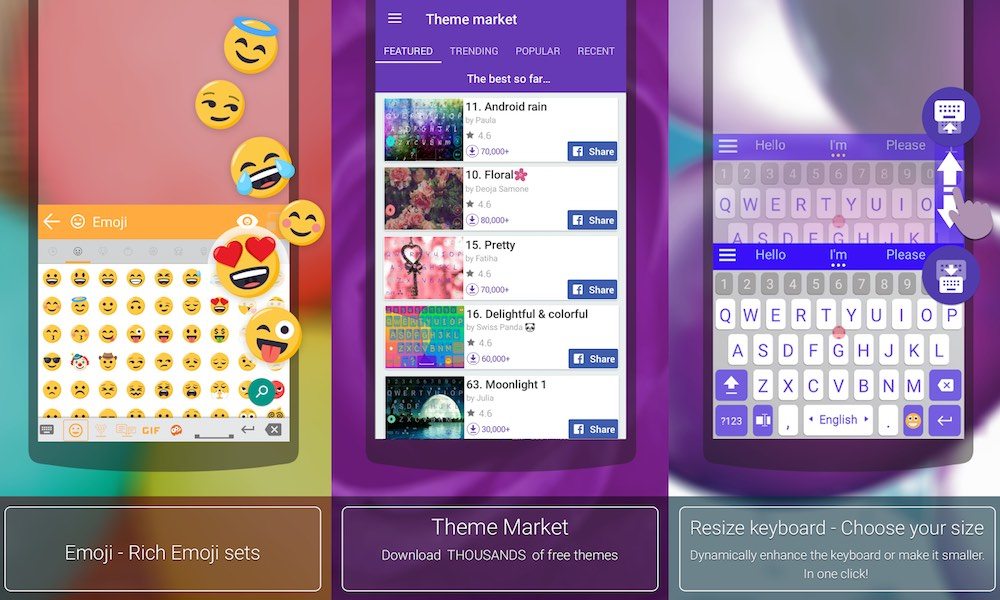
Ai.Type is a customizable keyboard app for Android and iOS boasting about 40 million users worldwide. When installed on a device, the app asks for “Full Access” — which includes absolutely any information or keystrokes typed through the keyboard. According to ZDNet, there’s evidence that the company had also recorded and stored text entered into the keyboard — though to an unclear extent.
The app also seems to have recorded data stored locally on a user’s device — such as their contacts’ emails and phone numbers. According to Kromtech, researchers found that 6.4 million users had had their contacts data collected, which amounted to 10.7 million email addresses and 376.4 million phone numbers within the records.
Ai.Type, for its part, tells a slightly different narrative. The company’s CEO, Eitan Fitusi, told the BBC that the stolen information was a “secondary database,” that IMEI data was never collected, and that the location data wasn’t “accurate.” Ai.Type did not deny that the database was publicly available for a period of time, but added that it has since been secured.






