Researcher Says iOS 12’s Security Code AutoFill Is a Security Risk
 9to5Mac
9to5Mac
Toggle Dark Mode
Apple’s iOS 12 update includes a new “Security Code Autofill” feature that could potentially become a vulnerability for users.
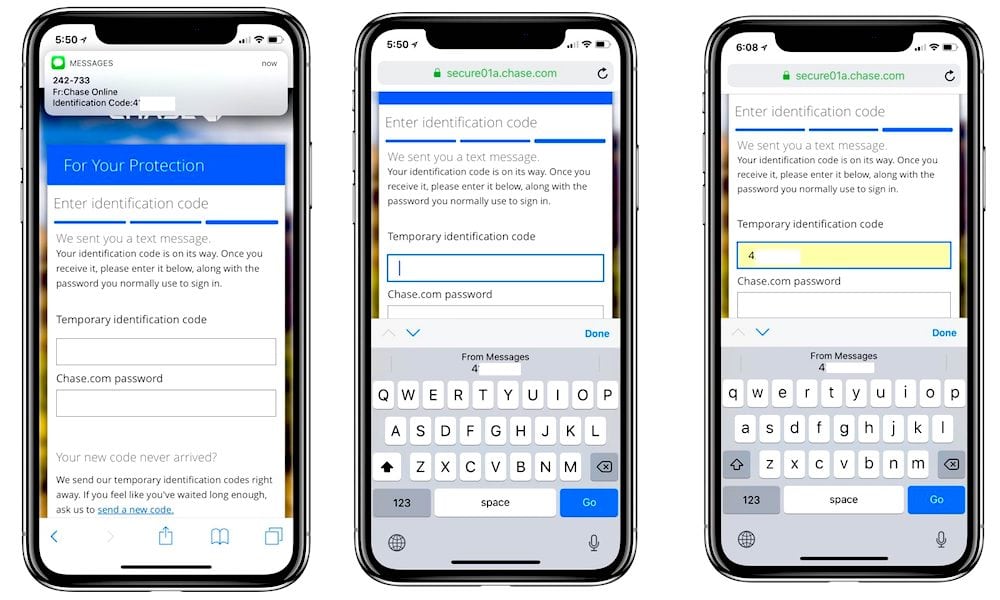
The feature is meant to make two-factor authentication via SMS easier and more seamless. When an entity — like a website or a bank — sends a one-time security login code to a user’s phone, it will automatically appear as an AutoFill suggestion.
This means that users won’t have to try and quickly memorize the code as it appears in a notification, or switch between apps to type it in. Essentially, it makes two-factor SMS authentication a “one-tap” process.
But while convenient, the new feature has one researcher concerned about the implications.
What’s the Issue?
Andreas Gutmann, an information security researcher at University College London, contends that the new feature could expose users to an increased risk of banking fraud.
Specifically, Gutmann wrote in a blog post this week that Security Code AutoFill could “negate” the security benefits of transaction authentication — a type of two-factor authentication commonly used by banks and financial institutions.
It’s meant to protect users against various malicious methods like phishing or Man-in-the-Browser malware attacks. These attacks can also rely on social engineering tricks that could trick users into sending unauthorized transactions.
Oftentimes, it works by sending a summary of a large transaction and a two-factor authentication to a user’s mobile device via SMS. To verify that the transaction is legitimate, users need to type in the security code into a webpage.
But Security Code AutoFill removes the most important aspect of this type of two-factor security: human validation. By making it a one-tap process, users could potentially input a security code without properly reviewing its attached message and context.
Gutmann adds that, unless the new feature can reliably distinguish between one-time login codes and transaction authentication codes, it could mistake one for the other. Again, possibly inputting a code without any of the details of the transaction.
“The fact that a user verifies this salient information is precisely what provides the security benefit,” Gutmann wrote. “Removing that from the process renders it ineffective.”
The end result may be attacks that allow malicious entities to make unauthorized transactions by tricking users into quickly inputting a two-factor authentication code. Gutmann writes that this could come about thanks to Man-in-the-Middle attacks or malicious websites.
SMS-based two-factor authentication is already a relatively insecure form of security, but it’s certainly better than nothing.
While the researcher said he and his colleagues are “excited” that Security Code AutoFill could encourage more users to adopt better security measures, he still cautioned against the potential for abuse.
Gutmann recommends that banks continue to educate their customers about verifying transactions and implement biometric authentication measures. He also thinks Apple should turn off Security Code AutoFill for transaction authentications.






