The Green Bubble Finally Gets a Lock: iOS 26.5 Ends the RCS Privacy Gap

Toggle Dark Mode
Apple has just released iOS 26.5, and while there aren’t a ton of new features at this stage of the game (after all, iOS 27 debuts in less than a month), there are still at least 50 good reasons why you should install it right away — and almost all of them are related to security in one way or another.
At the top of this list is a new user-facing feature that promises to make your communications more secure when chatting with Android users in Messages — and it’s a big enough deal that Apple posted a newsroom announcement about it. That’s a rare move for any point release, but especially for a “.5” release.
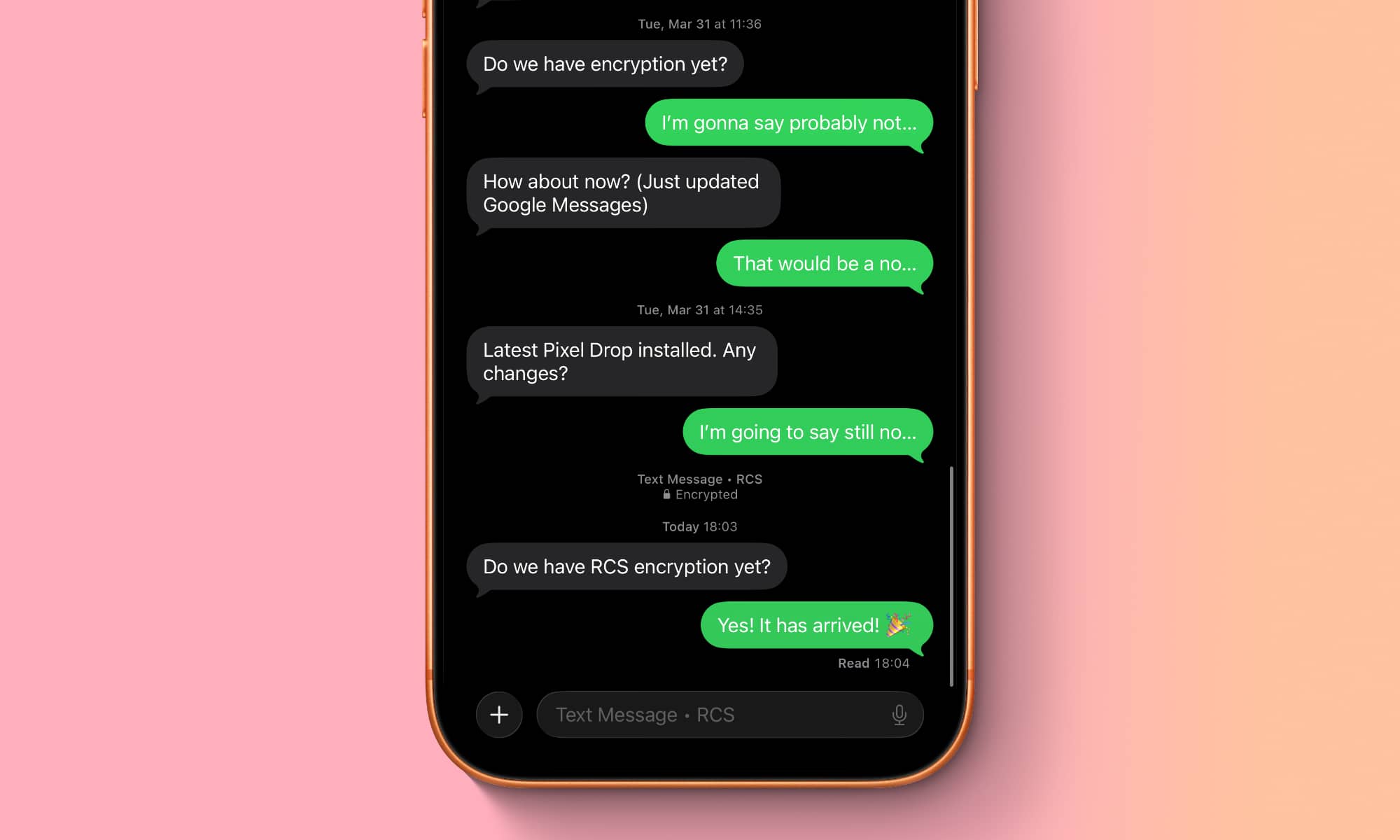
Starting today, end-to-end encrypted RCS messaging begins rolling out in beta for iPhone users running iOS 26.5 with supported carriers and Android users on the latest version of Google Messages. When RCS messages are end-to-end encrypted, they can’t be read while they’re sent between devices. Users will know that a conversation is end-to-end encrypted when they see a new lock icon in their RCS chats. Encryption is on by default and will be automatically enabled over time for new and existing RCS conversations.
Apple
While Apple is still calling this a “beta,” that appears to be more about challenges with widespread availability than any limitations in iOS. As Apple notes, it’s not available on every carrier just yet, and Android users will need to ensure they’ve updated to the latest version of Google Messages before they can play along.
Fortunately, Apple has taken some of the guesswork out of figuring out which carriers are on board. Now that iOS 26.5 is available to the public, it’s updated its carrier support page to include “End-to-end Encrypted RCS messaging (beta)” for those that are compatible with the new RCS profile.
The good news is that this includes all of the major North American carriers — and quite a few of the smaller ones, too. In fact, most of the ones that aren’t on the end-to-end encryption (E2EE) list are left out simply because they don’t support RCS at all. In fact, the only ones that support RCS messaging without E2EE are H20 Wireless, Total Wireless, and Canada’s Tbaytel.
The situation with Android is a bit more complicated, as you might rightfully assume you should already be able to engage in E2EE RCS chats with anyone on Google Messages. After all, Google has supported RCS E2EE for years. However, there’s a catch here that’s a bit counterintuitive: Google’s RCS encryption implementation was entirely proprietary, which is the whole reason Apple wasn’t on board with it.
It wasn’t until the GSMA — the group that oversees the RCS Universal Profile — announced an E2EE standard known as Message Layer Security (MLS) that Apple promised to embrace it. However, Google also had to do the same for interoperability, and while it’s already had that in beta for a few months, it’s only recently been released to the public as part of a Google Messages update.
So, don’t be surprised if you’re not getting encrypted communications with all of your Android-toting friends right away — even if you’re both on compatible carriers. At the very least, you may need to encourage them to update their Google Messages app, but there may also be some on older phones that don’t have that option (in much the same way the iPhone XR and iPhone XS will be left out of E2EE RCS as they can’t be updated to iOS 26).
The Other 50 Reasons to Install iOS 26.5
While iOS 26.5 adds a few smaller features and tweaks, it also fixes a staggering number of security vulnerabilities.
Apple’s security release notes list over 60 Common Vulnerabilities and Exposures (CVEs) that have been fixed in iOS 26.5. While a few of those overlap, there are still more than 50 distinct security issues, and it’s a list that’s serious enough that Apple has also released iOS 18.7.9, iOS 16.7.16, and iOS 15.8.8, along with their iPad equivalents. There’s also iPadOS 17.7.11 which is applicable only to Apple’s tablets as there are no iPhones that can run iOS 17 that can’t also be updated to at least iOS 18.
While the silver lining is that Apple isn’t aware of any of these having been exploited, these security release notes become a laundry list for hackers to find new ways to exploit iPhones and iPads that haven’t been updated to the latest iOS release, making it more dangerous than ever to stay behind. Put simply, if the cybercrooks of the world didn’t know about these vulnerabilities and exploits before, they certainly do now.