iCloud Private Relay | What Is It and What Does It Do? How Does It Work?
 Jesse Hollington / iDrop News
Jesse Hollington / iDrop News
Toggle Dark Mode
When Apple took the wraps off iOS 15 last month, it also shared one of the biggest upgrades to iCloud that we’ve seen in years — a new iCloud+ service that will offer even more features to protect user privacy.
This includes Hide My Email, an expansion of iOS 13’s Sign in with Apple that allows users to easily set up dynamic private email addresses on the fly, instead of only when signing in to supported services with your Apple ID. Best of all, you don’t need an iCloud Mail account to use it.
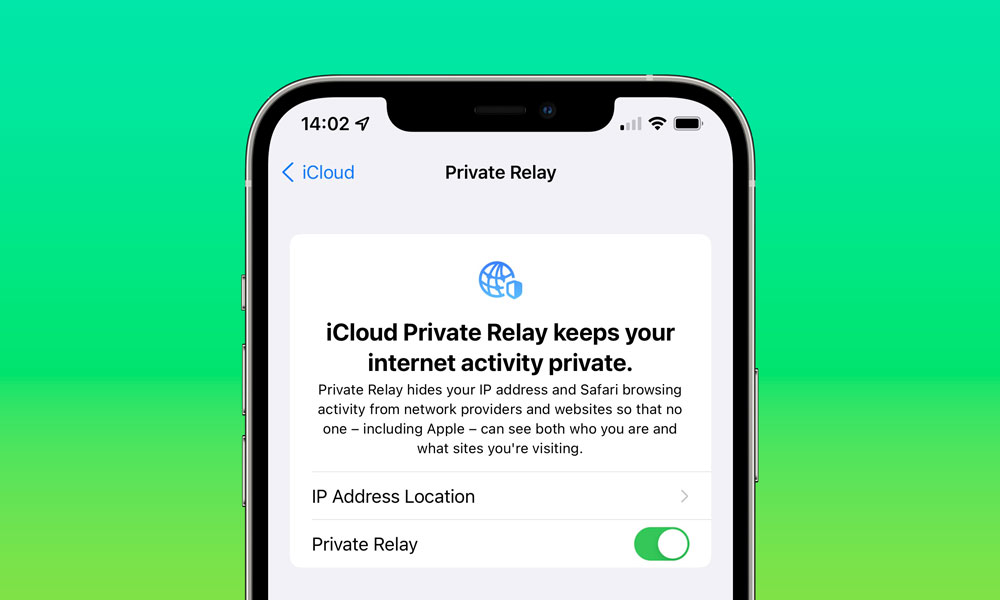
Perhaps more interesting, however, is iCloud Private Relay, a VPN-like service that will help to protect your online identity by completely obscuring your IP address while browsing. But it’s not perfect.
What’s iCloud Private Relay? What Does It Do?
In true Apple fashion, iCloud Private Relay is even better than a traditional VPN, since it’s set up in such a way that not even Apple will be able to track where you’re going.
You see, while most VPN providers promise to obscure your real location both from your ISP and from those sites that you visit while surfing through the VPN, the company providing the VPN service generally knows exactly what you’re doing. There’s also not much you can do about this, other than trusting their privacy policies. This is why it’s important to choose a reputable VPN provider.
On the other hand, Apple has very cleverly build iCloud Private Relay with a “zero knowledge” design by using two separate internet relays that are at arms length from each other.
iCloud Private Relay is a service that lets you connect to virtually any network and browse with Safari in an even more secure and private way. It ensures that the traffic leaving your device is encrypted so no one can intercept and read it. Then all your requests are sent through two separate internet relays. It’s designed so that no one — including Apple — can use your IP address, location, and browsing activity to create a detailed profile about you.
Apple
As Apple’s internet technologies engineers Tommy Pauly and Delziel Fernandes explained at WWDC, Apple will be routing Private Relay traffic through two proxy servers — one owned by Apple, and another one owned by a content provider.
Just like a VPN, all the traffic that passes through iCloud Private Relay is encrypted, and the first proxy server in the chain — the one owned by Apple — is the only one that knows your original IP address. However, this server, also known as the “ingress proxy”, doesn’t need to decrypt or inspect your surfing traffic — it simply passes everything on to the second “egress proxy” server.
However, since this next proxy server gets all of its traffic from the first one, it doesn’t get to know where that data originally came from. The egress proxy server opens up the packets, figures out their ultimate destination, and establishes the connection.
This means that, when using iCloud Private Relay, no one server ever knows both who you are and where you’re going.
Traffic that leaves the egress server naturally comes from an IP address that’s not directly connected to you, however you’ll be able to decide if you want to use an address that reflects your general location (e.g., your city or region), so that you can still have local content like news and weather more easily delivered to you.
Alternatively, you can tell iCloud Private Relay to use a more generic IP address that’s simply somewhere in the same time zone within your home country, so that websites you visit won’t even know what city you’re in, much less a more specific neighbourhood location. That said, it’s important to keep in mind that may not help if you live in a major metropolitan area, as many of the general country-level egress IP addresses are already located in those areas.
What Private Relay Won’t Do
As magical as this all sounds, there are a few important limitations to be aware of when it comes to how iCloud Private Relay will work — and some reasons why you might even still prefer a traditional VPN.
- iCloud Private Relay will not bypass geographic restrictions. The IP address set by the egress server will always be somewhere in your home country. You’ll need a traditional VPN if you want to sneak around geo-blocking to access services like Netflix, Hulu, and Amazon Prime Video while travelling abroad.
- For the most part, Private Relay only protects your web browsing. While a VPN can handle all of your internet traffic, iCloud Private Relay is designed to protect your web browsing. All traffic that originates from Safari will be protected, and Apple will also encrypt all DNS name resolution queries — those requests that turn names like “www.idropnews.com” into numerical IP addresses. Beyond that, however, Apple says it only protects a “small subset of traffic from other apps,” designed to prevent them from “unintentionally leaking user information or exposing users to security attacks.”
- Local Network Traffic isn’t encrypted. If you’re using your iPhone, iPad, or Mac to access internal websites at your business or school campus, these won’t be handled by iCloud Private Relay at all. Only traffic that goes out onto the public internet passed through Apple’s iCloud Private Relay servers.
- VPN Traffic takes priority. If you’re already using a VPN, then all of your traffic will get routed through that VPN service provider instead. In fact, depending on how they’re set up, some VPNs may cause iCloud Private Relay being disabled entirely while the VPN is up and running.
- Individual apps can bypass Private Relay. By default, Apple will protect all web-based traffic that leaves your device, even if that comes from third-party apps. However, if an app uses a specific proxy server or adds its own VPN capabilities, that traffic won’t travel through the iCloud Private Relay service.
- Using Private Relay will bypass your router’s parental controls. Since all the traffic is encrypted before it leaves your iPhone, iPad, or Mac, even your home router doesn’t know where you’re going — so it can’t stop you from going there either. This doesn’t affect Apple’s Screen Time and other on-device parental control apps, however, as these filter traffic before it gets to iCloud Private Relay.
- Businesses and schools can block iCloud Private Relay. This may be necessary for organizations that are required to monitor all network traffic, or enforce other restrictions on their users. In this case, you’ll be clearly told that iCloud Private Relay has been disabled, so you won’t be taken by surprise, but this also means you won’t be able to benefit from its privacy and security features. If this is happening at your employer or school, it’s probably fair, but if you see this happening on a public Wi-Fi network at your favourite coffee shop, it’s probably a good idea to stop using their free Wi-Fi.
Lastly, iCloud Private Relay is a feature of Apple’s new iCloud+ tier, which is really just a way of saying that you have to be a paying iCloud subscriber to benefit from it. However, iCloud+ will be the new normal for all the current iCloud storage plans — at no additional cost — so even if you’re only paying $0.99/month for the 50GB package, you’ll be able to benefit from it.
Even for users who aren’t paying, however, iCloud Private Relay will still be used to handle all traffic associated with trackers and advertising networks.
This part of the feature is intended to build on the App Tracking Transparency feature that Apple added in iOS 14.5, by closing the door on yet another method known as “fingerprinting” that many advertising networks use to track your activity as you move around the web. While most ISPs will assign a dynamic address to your home router, this doesn’t change very often, so ad trackers will use this information to follow you around. This lets them tie together the products you buy on Amazon, the pages you like on Facebook, and the things you search for on Google.
With iCloud Private Relay, however, these trackers never get to see your actual IP address. Of course, they still get an address, but it’s an address that’s going to be shared with every other iCloud Private Relay user in your region, making it effectively useless for any kind of fingerprinting.






