11 Most Common and Dangerous Apple Scams in Circulation
 CFD Optie Brokers
CFD Optie Brokers
Apple is well-known for its commitment to user privacy, and its devices have a reputation for being incredibly secure and resistant to viruses. Across the board, that’s a reputation that’s well-earned.
But despite that, users of Apple devices and platforms can still be prone to scams — malicious attacks that prey on user trust to solicit sensitive information, login credentials or even financial details.
This isn’t strictly an Apple problem; scams exist across all tech platforms, but they’re notable because they can affect users of Apple’s normally secure platforms.
Use the right arrow to browse 11 of the most common Apple-related scams — and what you can do to protect yourself.
11 Fake Receipt or Invoice Scams
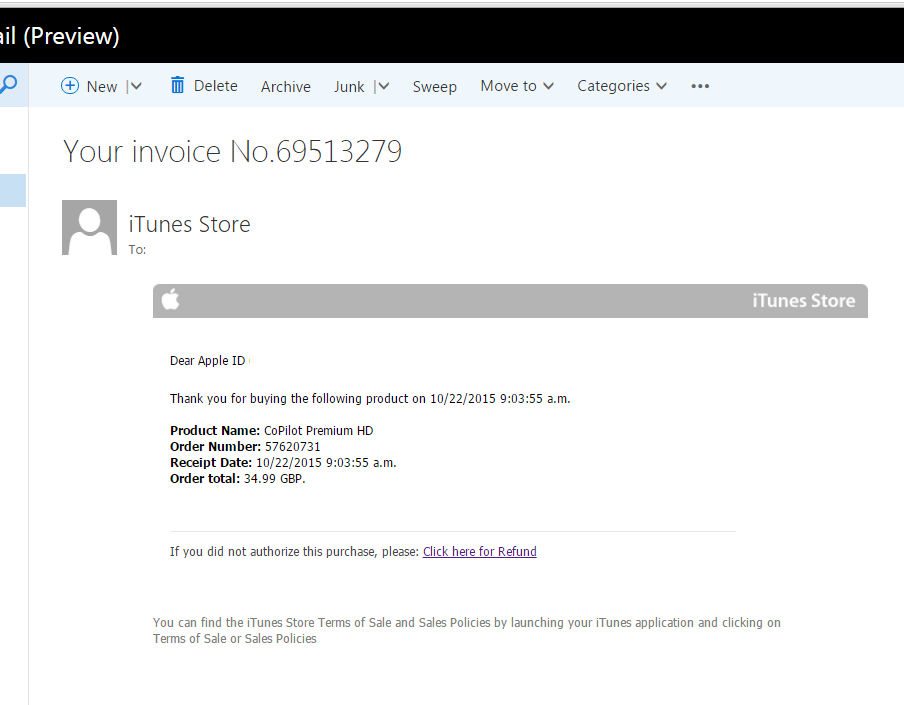
Some recent Apple scams take an evil but clever twist. Rather than asking a user for information or to make a purchase, these scams claim that a user — or a malicious third-party — has already made a purchase.
These scams appear to be official Apple receipts or invoices, and they can be extremely convincing. More often than not, they’ll simply claim that the recipient has made a recent purchase (typically a large one). Of course, since the victim hasn’t bought whatever is on the recipient, they’ll quickly look to cancel or report the fake purchase.
The fake receipt will have a link to cancel if the purchase if it was unauthorized (which, of course, it was).
When clicked, it’ll bring users to a page asking for their name, Apple ID and password, address, birthdate, social security number, and financial information.
Apple users should be aware that the company will never ask for your sensitive information when canceling a purchase. It’s also smart to keep an eye on the sender’s email, as well as the link (you can hover over the “cancel purchase” link to see its true destination).
If there’s even a trace of doubt in your mind, delete the email and contact Apple.
10 Phone Call Scams

While actual phone call scams may be falling out of fashion in favor of texts and emails, they still do happen from time to time. So it’s important that Apple and other tech users remain vigilant so they can avoid them.
Typically, the scam caller will purport to be an Apple service technician or Apple Support staff. They’ll explain that there’s been a “breach in the system,” or that a user’s iCloud account has been locked for one reason or another.
At this point, the scammer will ask a user for their personal information to “verify their account.” This can encompass a wealth of data, and typically includes a user’s login credentials or financial information.
To avoid phone call scams, first off, don’t give anyone your personal information over the phone if it’s an unsolicited call. If you receive a call from someone claiming to be from Apple, the company recommends hanging up and contacting them directly.
9 An Email from “Apple”
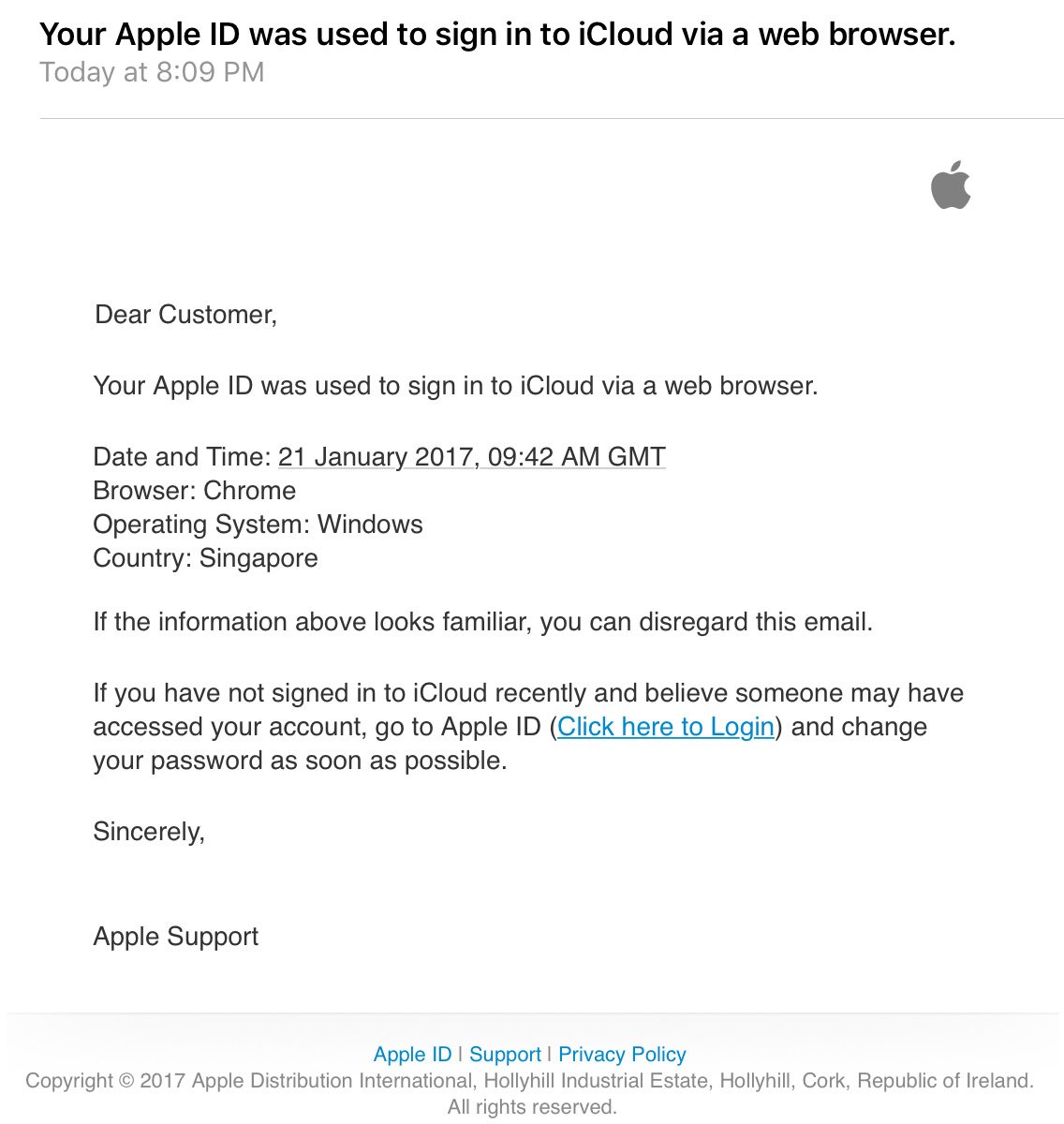
For most Apple users, an email from Apple isn’t a cause for concern. In fact, it’s usually a common occurrence. You can get a variety of emails from the Cupertino tech giant for various actions. That’s the issue with email scams.
Worryingly, many email-based scams are also frighteningly realistic. As with the invoice or receipt scam mentioned earlier, these can be a near carbon copy of an email you might actually receive from Apple or another tech company.
All of these scams will present a problem, such as your Apple ID being “locked” or a change in Apple’s “security policies.” As with basically every other tech scam, the malicious email will claim that your personal information is needed to fix the issue.
In most cases, they’ll take you to a page that also appears to be legitimate, where they hope you’ll enter your sensitive data.
As always, check the email’s sender and the body text of the message. Inconsistencies are fairly easy to spot. Similarly, be aware if any email is asking you to input your personal information — the majority of legitimate emails won’t. When in doubt, delete the email and contact Apple directly.
8 iMessage Scams

With the rise of the smartphone, scams delivered via iMessage or SMS text are becoming increasingly common. In our digital era, you’re just as likely to receive a scam through text as you are through an email.
As with previous scams on the list, text scams can vary in form. They’ll say that your Apple ID has been locked due to a recent string of attempted logins, or something similar. They can also claim that your Apple ID will soon be terminated, or that your iCloud account has been closed for some reason (which, at times, isn’t given).
Most scam text messages will promise dangerous consequences if you don’t comply (though, of course, the exact opposite is true), and will include a link to a fraudulent site where you’ll input information. Some scams even incorporate other random text messages in a foreign language to give their claims of a “breached account” extra credibility.
As with other scams on this list, your best bet to deal with unsolicited contact is simply to delete the message. If they mention texting them back to stop further texts, don’t. Doing so will tip the scammers off that they have an active, real phone number to harass in the future.
7 Browser Pop-Up Scams
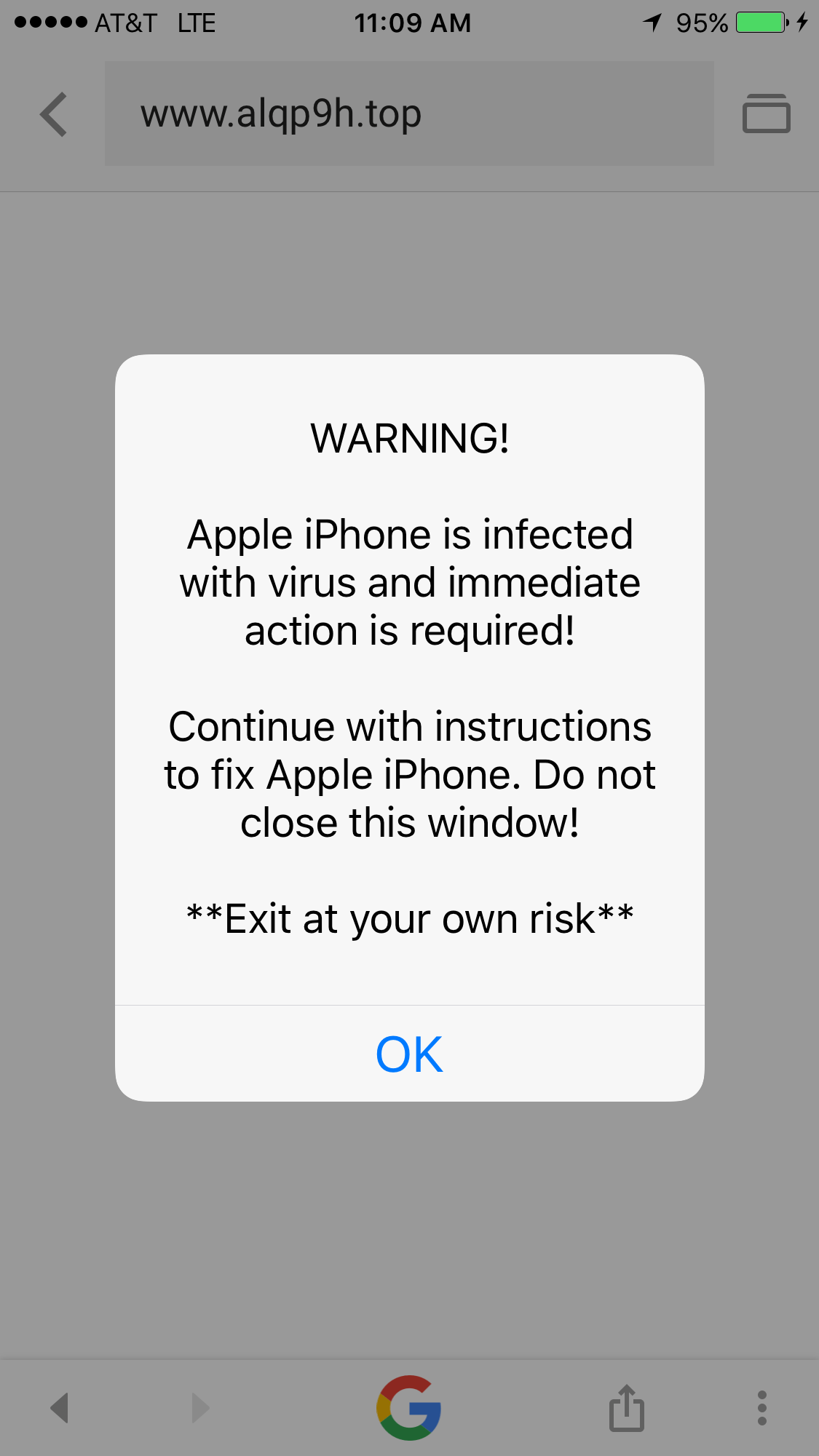
If you’re an iOS user, this might very well the scam that you are most familiar with. You’ve probably seen a random pop-up when browsing various sites on your iPhone or iPad, and they’ll share the same sense of urgency as previous scams.
These scams will claim that your iPhone has a virus (not likely), is in the process of crashing (a pop-up won’t appear for a crash), or that there’s another assorted problem with your iPhone. Annoyingly, it’s not always easy to close out of them — in some cases, they’ll even reappear if you exit out of and re-open your browser.
Sometimes, they’ll tell you to contact “tech support” and will provide a fake phone number. Other times, they’ll redirect your web browser to a scam website that’ll attempt to solicit your personal information or login details. As always, exercise caution when someone’s asking for your sensitive data.
The best way to deal with these types of scams is to close your web browser. In some cases, you might have to hit “OK” and quick exit out of the affected tab.
You can always go into settings for Safari or Chrome and disable website popups — this is perhaps the only way to deal with these scams in advance although legitimate and useful pop-ups will also be blocked.
6 In-App Purchases Scam
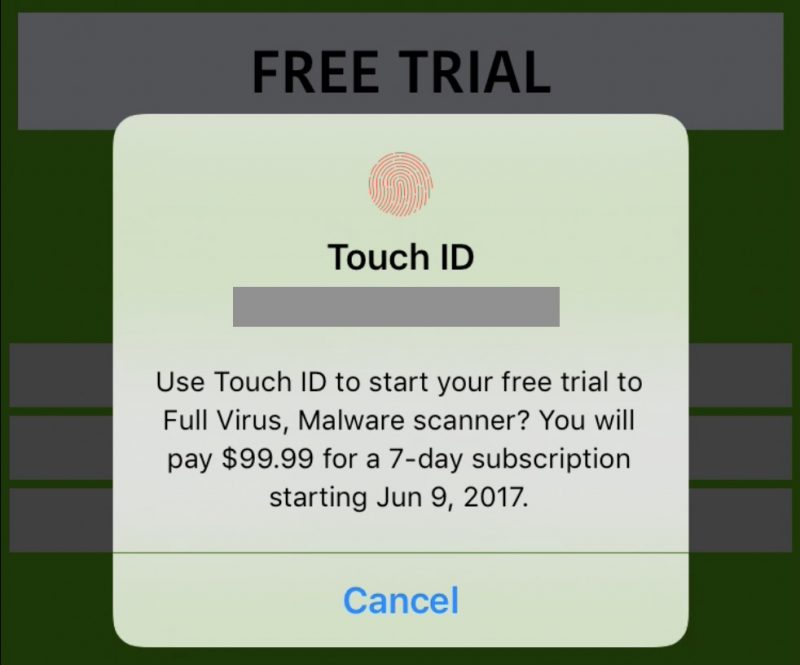
Some scams don’t utilize consumer-company trust. Rather, they abuse app developer-customer trust by creating fake applications that, basically, ask for money in return for a service.
Apple is typically pretty good at keeping malicious apps out of its App Store, but it’s within the realm of possibility for some to get through the review process. Because of this, it’s still important to be aware and remain vigilant — as one developer and writer pointed out last summer.
He discovered a fake “security & VPN” app that uses Apple’s in-app purchase system. In exchange for a (typically steep) subscription fee, these fake apps claim to provide some sort of fake service — such as anti-virus scanning or VPN system. Due to bugs in the App Store algorithm, they can appear fairly high in storefront search rankings.
If you’re worried about these types of scams, then keep an eagle eye out for questionable app titles with typos or inconsistencies and check the app’s reviews. Also, check the service that the app claims to provide. Note that iOS doesn’t need anti-virus software, and if you’re looking for a VPN, make sure that the VPN app in question is legitimate, vetted and well-rated.
5 iCloud Phishing Scams
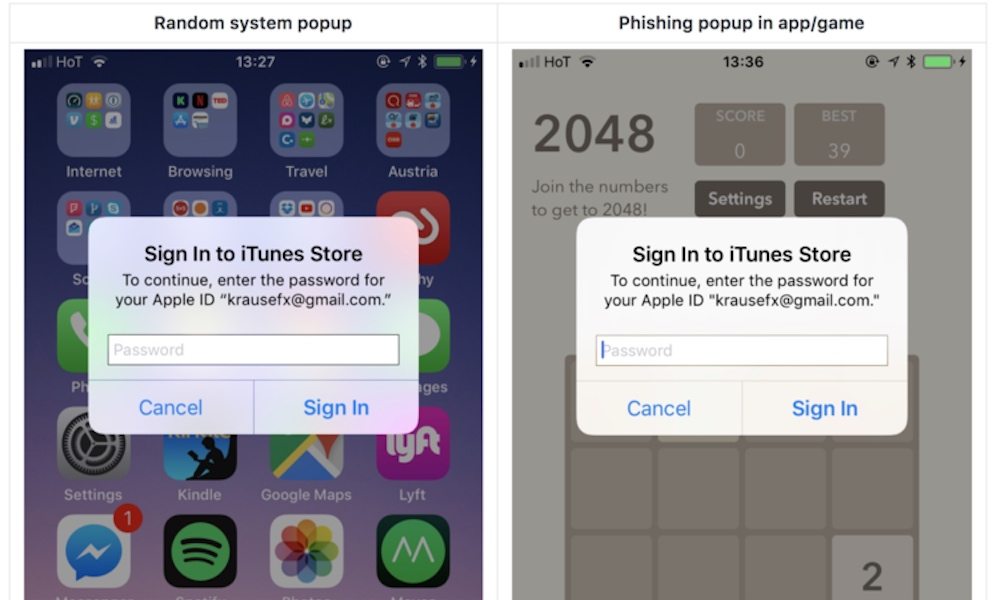
While browser pop-up scams are more common and annoying, they’re not the only kind of iOS device scam that uses a pop-up window. There’s another kind that’s much more malicious — particularly as it’s harder to check for legitimacy.
If you’re an iOS user, you’re probably familiar with OS pop-ups asking for your iCloud password to authenticate. Unfortunately, these pop-ups are shockingly easy to replicate on the developer side, as a security researcher revealed last year. Worse still, they can be nearly identical to legitimate password prompts.
Since iOS is a closed system, third-parties can’t issue a password prompt on the Home or Lock screen. But malicious entities can force a fake login popup within an app that’s been compromised or has been specifically created by an attacker.
These malicious prompts will attempt to steal ("phish") your iCloud password, and possibly your associated email address.
Luckily, Apple has a plan to mitigate these phishing scams in the future. In the meantime, your best bet is to hit the Home button.
- If the popup goes away on the Home screen and doesn't reappear, it’s a scam.
- If it remains on the screen then it’s a legitimate password prompt.
4 iTunes Gift Card Scam

Not all Apple-related scammers pretend to be employees. Other scams, like a recent string of gift card fraud, simply ask for payment via iTunes gift cards. Still, these are related to Apple’s platforms, and it’s worth taking note of them.
The scams can vary in form, but they all follow a familiar pattern. Typically, one will receive a phone call from a scammer that instills a sense of panic. They can claim to be debt collectors, bail bond companies, or even the Internal Revenue Service coming for tax funds.
No matter who they pretend to be, these fraudsters will demand that a user buy an iTunes gift card, or other gift cards from another store, to use as “payment” for whatever debt they claim to be owed. They then ask the victim to provide them with the 16-digit gift card code over the phone.
This may go without saying, but the IRS and similar official organizations have no reason to only accept gift cards as payment.
If you receive any sort of phone call mentioning gift card payments, ignore them and report the fraudsters to the local authorities or even the federal government.
3 Locked Device Ransomware
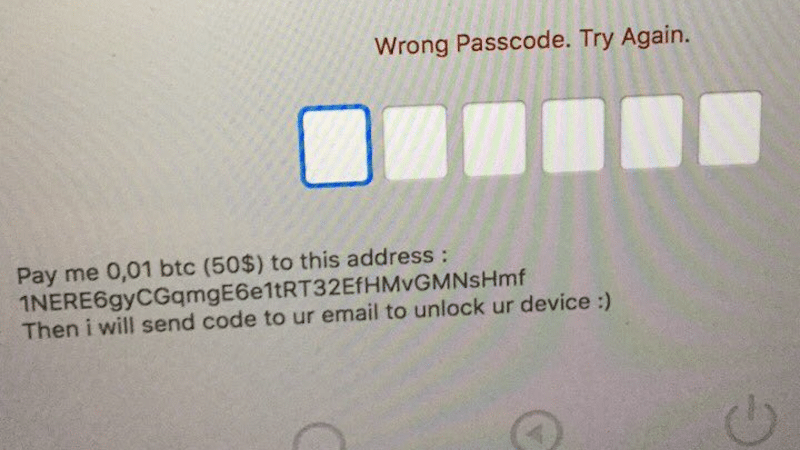
This is, admittedly, more of a case of ransomware than an actual scam. Similarly, it’s less common than other scams on this list. But it is perhaps the most malicious attempt at getting money out of users that we’ve seen.
The scam relies on Apple’s Find My iPhone or Find My Mac feature. Essentially, attackers with access to a user’s Apple ID or iCloud login credentials can — theoretically — lock a Mac or iPhone, display a message, and demand payment to unlock the devices. The scammers can then threaten to wipe the device entirely if payment isn’t received.
It’s worth noting, at this point, that an Apple user can fall victim to this ransom scam if they’ve given out their login details in another scam on this list. Worse still, there’s little a user can do to fix the situation on their own — in most cases, contacting Apple is the only course of action.
The best way to avoid this scam is to use distinct and strong passwords for each and every internet service you use. Don’t re-use passwords. Similarly, it’s recommended that you enable two-factor authentication. If the unthinkable has already happened, then as stated above, contact Apple.
2 "Tech Support" Scam
Tech support scams aren’t Apple platform-specific, but they can be deployed on web browsers running on macOS and other Apple operating systems.
Unlike scams that seek a user’s passwords or login credentials, many tech support scams are more often after something else: your hard earned cash.
Tech support scams rely on a variety of methods for fooling users that they are, in fact, associated with a large tech company or tech support firm. These can range significantly in form and function, but the best example is a Chrome-based scam discovered earlier this month.
The scam attacks Google Chrome, using an exploit to freeze the browser. A fraudulent error message will then appear, prompting users to call a fake tech support number and, presumably, disclose their financial information to “fix” the issue.
The best way to avoid a scam like this is not to panic. Actual tech support personnel won’t prompt you to call them via random error message in a web browser. Simply force-quit your Browser, or if applicable, close out of the affected tab.
1 Flash Installer Malware
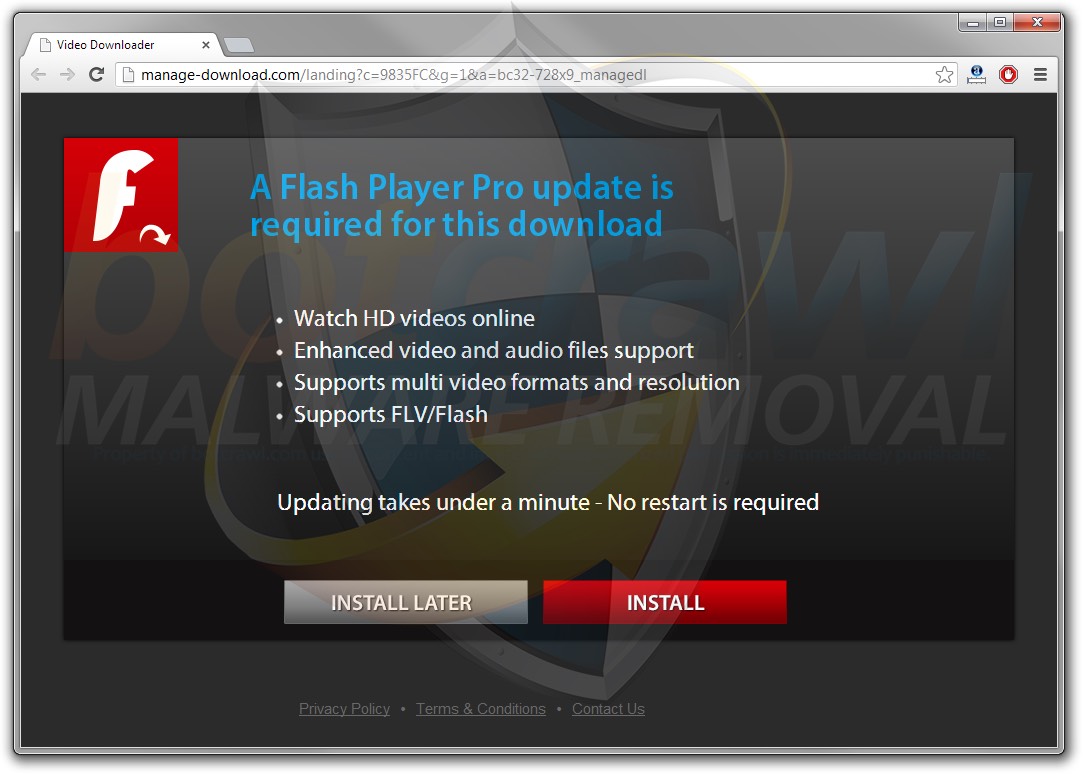
Most scams are, essentially, confidence tricks. They abuse the trust between consumer and company to steal login information or financial details. But some scams use that trust to perform other malicious activities.
A good example is a backdoor malware that masquerades as a legitimate software program. In 2017, security researchers discovered that such a malware — dubbed “Snake” — had made its way from Windows to Mac-based platforms.
Snake appears to be a legitimate Adobe Flash installer, and in fact, it does actually install Adobe Flash. But it also laces the download by installing additional malicious software that can provide a backdoor into your Mac platform — allowing hackers access to your sensitive data. It is a classic definition of a trojan horse malware.
Apple has since revoked the Snake’s fraudulent developer certificate, but similar malware could still pop up. The best way to avoid them is to only allow downloads from the Mac App Store, or from developers and sources that you truly trust. If you need Adobe Flash, for example, download it directly from Adobe.
