Zoom’s Video Call App Could Be Spying on You, Even After You’ve Uninstalled It — Here’s How to Eradicate All Traces of It
 Lewis Ngugi
Lewis Ngugi
Toggle Dark Mode
A serious new security vulnerability has been discovered in Zoom’s Video Conferencing app that has left millions of Mac users exposed to a flaw that could allow any website they visit to turn on their FaceTime cameras without their permission.
The vulnerability, which was first reported by software engineer Jonathan Leitschuh yesterday, basically allows any website to forcibly join a user to a Zoom call, with their camera activated, without any indication at all to the user as to what is going on.
In fact, in addition to the obvious privacy impact of this flaw, a secondary aspect is that any webpage could hangup a user’s Mac simply by “repeatedly joining a user to an invalid call.”
Zoom’s video conferencing app isn’t some small, fly-by-night service either. It’s used by 750,000 companies around the world to conduct their business, including such big names as Nasdaq, the U.S. Centers for Disease Control and Prevention, the U.S. Department of Homeland Security, and the U.S. Department of Energy.
But It Gets Worse
If you have ever installed the Zoom client on your Mac — even if you’ve completely uninstalled it — you’re still very likely vulnerable to this massive security flaw. In a move that Daring Fireball’s John Gruber justifiably describes as “criminal”, it seems that Zoom leaves dangerous pieces of itself behind, in the form of a local web server, even after a user would have every reason to believe they’ve uninstalled it.
Additionally, if you’ve ever installed the Zoom client and then uninstalled it, you still have a localhost web server on your machine that will happily re-install the Zoom client for you, without requiring any user interaction on your behalf besides visiting a webpage. This re-install ‘feature’ continues to work to this day.
Jonathan Leitschuh, software engineer and security researcher
This local web server not only keeps running in the background, but actually re-installs the Zoom client, in the background, as soon as the user’s Mac gets a request for a video call — a request that can easily be buried in a malicious web page.
To make matters even worse, Zoom itself appears to be unapologetic about this vulnerability, having done nothing to fix it after Leitschuh reported it back in March. In fact, according to BuzzFeed News, the company did release a fix for an unrelated flaw, but conspicuously left the camera issue unaddressed.
While Leitschuh classified the severity of the issue as an 8.5 out of 10 when he first reported it to Zoom, the company itself reviewed it and re-categorized it as only a 3.1, and simply said that it was “evaluating options” to add a feature that would require users to confirm whether they want to join a meeting or not.
Zoom Will Fix the Flaw, But Not the ‘Feature’ Behind It
While Zoom has now committed to releasing a patch for the vulnerability by July 11, the company has said that it has no plans to change the behaviour of running a phantom web server on users’ computers, explicitly stating that it is “not a security concern.”
We consciously enabled the ability to have meeting joins initiated from within an iframe on a webpage. That’s not a security concern.
Richard Farley, Chief Information Security Officer for Zoom
Zoom also told BuzzFeed News that it doesn’t even plan to add a dialog window to simply ask users if they would like to join a meeting after clicking an invite link. In fact, Farley pointed the finger at Apple as the reason for the background web server, saying that it was built as a “workaround” after Apple made a security change in Safari 12 to improve user privacy, in order to avoid making users click an extra dialog box before joining a meeting. It seems that Zoom thinks that asking a user if they want to join a meeting is a “poor user experience.”
Per their own statement, Zoom made a set of product decisions that intentionally prioritized use of their system over user choice. Zoom clearly had not considered malicious uses — or, worse, had disregarded them — when they decided to remove this choice from the user, and appear to consider Zoom use, and presumably their revenue growth, more important than surveillance of users.
Eleanor Saitta, security consultant
The problem, of course, is that Zoom’s design decisions pave the way for security flaws in its software to be widely exploited, and while Zoom claims that it has heard no reports of this happening, Farley admitted that there’s really no way for them to know.
Meeting joins happen all the time. Millions a day. There isn’t really a way for us to look at the logs to determine whether that was an intentional join by the user or the user was phished into joining.
Richard Farley, Chief Information Security Officer for Zoom
How to Completely Remove Zoom
The problem here is that going through the normal procedure of removing Zoom will not remove the phantom web server that remains on your Mac, which again means that if you’ve ever installed Zoom on your computer, you’re technically still running it, regardless of whether you can see any signs of it or not.
Users who want or need to continue running Zoom can simply enable the option to “Turn off my video when joining a meeting”, but based on Zoom’s lack of concern for user choice and privacy, we’d certainly recommend taking steps to eradicate all traces of Zoom entirely — especially if you think you’ve already uninstalled it. Zoom has promised to patch this specific bug, but won’t be changing its behaviour of automatically joining users to meetings, nor will it remove its hidden web server from the Mac version of its client.
- If the Zoom client is still on your Mac, uninstall it by dragging the Zoom app from the Applications folder to the trash.
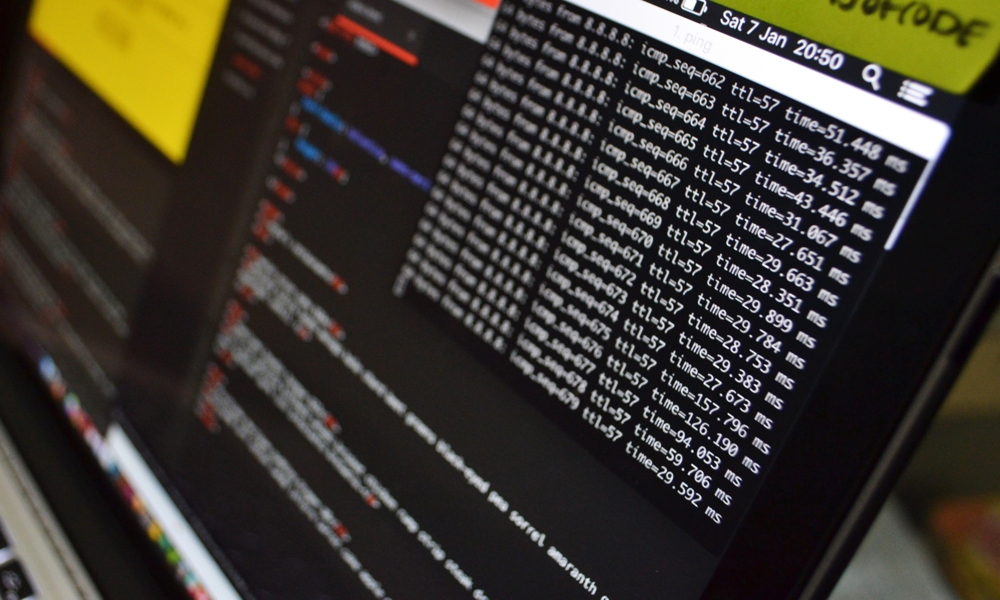
- Open the Terminal application on your Mac
- Type: lsof -i :19421 and press Enter
- From the response that appears, look for the number that appears underneath the word “PID.” This is the process ID number of Zoom’s phantom web server.
- type kill -9 followed by a space and the “PID” number (e.g. if the number from step 3 was “12345” you’d type “kill -9 12345”)
- type rm -rf /.zoomus to remove the web server application files.
- Empty your trash.
This will result in killing the hidden web server off entirely, although of course it will come back if you reinstall or update the Zoom app.






