Group FaceTime Spy Bug: 5 Things You Need to Know
If you've been following the news over the last day or so, you've probably seen a slew of headlines about a major FaceTime bug that could threaten your privacy. News of the bug spread like wildfire among tech and traditional media outlets, but for good reason. It was a serious threat to Apple user privacy. Continue reading to learn 5 Things You Need to Know About the Group FaceTime Spy Bug.
What's the Big Deal?
While security vulnerabilities are routinely discovered in all software updates, the FaceTime spotted this week is particularly concerning because of its ease-of-access and the privacy dangers it poses.
Essentially, the bug allowed anyone who made a FaceTime call to hear audio from a recipient — even if the call wasn’t accepted.
If the recipient
All of this is made worse by the fact that the recipient may have no idea that their privacy is being threatened. On the recipient’s screen, it looks like a call has yet to be accepted even if the other party is surreptitiously listening to their audio.
What Is Apple Doing About It?
If this bug has you freaked out, take a deep breath and don’t worry. As of the writing of this article, Apple has completely disabled the Group FaceTime feature to prevent anyone from taking advantage of the security flaw.
Group FaceTime is listed as “currently unavailable,” which means that no iOS or macOS user should be able to access it. Without Group FaceTime, there’s no way to access the vulnerability — so your privacy and data is safe.
Apple also said that it is aware of the issue and has “identified a fix” for the underlying bug. The Cupertino tech giant said the fix will be included in a software update “later this week,” though it’s not clear when exactly that might be.
What Causes the Bug?
It isn’t readily clear what the exact bug is, but it appears to be tied to the way that Group FaceTime handles multi-user calls.
The vulnerability is accessed when a caller FaceTimes another user but adds their own phone number as a “third” party to a Group FaceTime call. Group FaceTime appears to automatically connect the caller to themselves and the original recipient.
The bug also appeared to be device agnostic, since it has been demonstrated on a variety of iOS and macOS devices running the latest software. Because of that, it’s likely a flaw within the Group FaceTime feature itself.
When Did Apple Find Out?
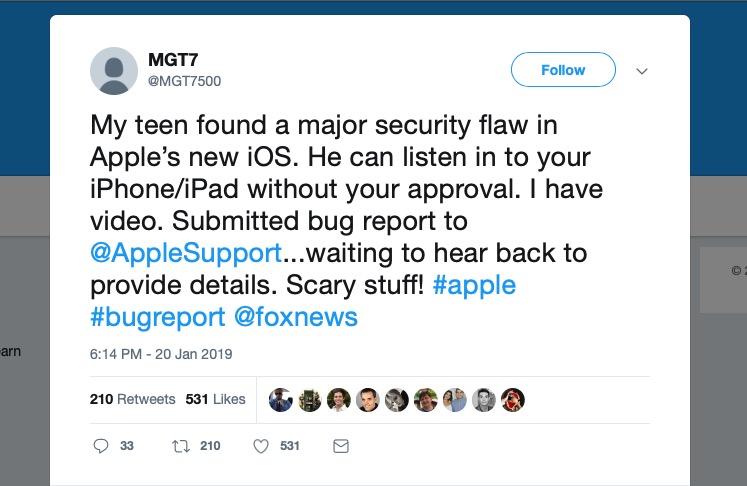
It isn’t clear when Apple was made aware of the bug, but it appears that at least one user attempted to notify the firm about it over a week ago. Twitter user MGT7500 tweeted at Apple Support, Tim Cook and Fox News in a series of tweets on Jan. 20 and 21.
In those tweets, the user said that her 14-year-old son had discovered a “major security flaw” that allowed users to covertly listen in on audio. The tweets are genuine, so it isn’t clear why Apple didn’t address the bug's existence sooner.
It’s possible that Apple was working on a fix but did not want to alert the public (and malicious third-parties) to the vulnerability by announcing it. Once word got out on Monday, there wasn’t anything Apple could do to mitigate its spread — except disable Group FaceTime.
Privacy Implications
The Group FaceTime bug came at a particularly inopportune time for Apple. For one, it was first widely publicized on Data Privacy Day. It also comes in the wake of recent Apple attempts to differentiate itself from its competitors based on its privacy policies.
But the bug isn’t at all indicative of Apple’s privacy stance. Because of that, users should treat it like any other major bug that may threaten their cybersecurity. To be clear, it's not a great win for user privacy, but it does appear to be an honest mistake in a piece of software.
Apple is still an outlier when it comes to how it handles users data. Unless Apple changes its position on how it handles user data (which isn't likely), the company is still one of the best producers of products and services for the privacy-conscious among us.